This page is intended to provide guidance regarding activities subject to export controls and typically overseen by the Export Control Compliance Program (ECCP). Topics and definitions are arranged alphabetically from A-Z. If you are unable to find an answer to your questions, please contact the ECCP at exportcontrol@unl.edu, or 402-472-6965.
As a reminder, your research or activities may be subject to export controls if you:
- Are shipping items internationally
- Will be traveling outside the U.S.
- Plan to have foreign national(s) participate in research or want to collaborate with a researcher or institution from outside the U.S.
- Are working on a project that has contractual restrictions regarding proprietary information, foreign national participation, publications restrictions, or that specifically includes export control regulations as a condition of the award, contract, or agreement.
- Will be receiving military or space related information, controlled unclassified/covered defense information, technical data, equipment or software, or will require a DD2345 form.
- Will be researching or working on subjects related to nuclear, chemical, biological, weaponry, missiles, or unmanned vehicle technologies.
- Working with encryption technology.
- Will perform work involving select agents or other pathogens.
List of Topics
Atomic Energy Act (AEA) Data – Tiers (1-3)
Cybersecurity Maturity Model Classification (CMMC)
Controlled Unclassified Information (CUI) & Covered Defense Information (CDI)
Critical and Emerging Technology
Dual-Use Research of Concern (DURC)
Embargoed or Sanctioned Countries with Special Rules
Entities on the Restricted List
Export Administration Regulations (EAR)
Export Control Classification Number (ECCN)
Export Controls & Biological Agents and Toxins
Fundamental Research Exclusion (FRE)
International Conferences and Presentations (Remote)
International Traffic in Arms Regulations (ITAR)
Military or Space Related Research
The Office of Foreign Assets Control (OFAC)
Online STEM courses to Sanctioned and Embargoed Countries
Participation in Research by Foreign Nationals
Publicly Available, Public Domain, and Open Source
Purchasing & Export Controls Guidance
Research Related to Nuclear, Chemical, Biological Weaponry, Missiles, or Unmanned Vehicles
Research Involving Select Agents or Other Pathogens
Research Related to Encryption Technologies
Restricted Party Screening (RPS)
Student Theses/Dissertations & Export Controls
United States Restrictions and Sanctions Related Lists (Consolidated Screening List)
Arms Embargo
The International Traffic in Arms Regulations (ITAR) prohibits exports, transfers and import of defense data, services and articles regulated under the ITAR to certain countries under a U.S. arms embargo or sanctions (22 CFR 126.1). It is the policy of the United States to deny licenses and other approvals for exports and imports of defense articles and defense services, destined for or originating in certain countries.
- For defense articles and defense services, the following countries have a policy of denial:
- Belarus
- Burma
- China
- Cuba
- Iran
- North Korea
- Syria
- Venezuela
2. For defense articles and defense services, a policy of denial applies to the following countries except as specified in the associated paragraphs under 126.1:
- Afghanistan
- Central African Republic
- Cyprus
- Democratic Republic of the Congo
- Eritrea
- Haiti
- Iraq
- Lebanon
- Libya
- Somalia
- South Sudan
- Sudan
- Zimbabwe
This means that, for UNL employees, shipping, sharing, or importing defense data or services with/from any of the above countries, including citizens of these countries, may constitute a violation of U.S. export control law. Appropriate approvals, where applicable, must be in place prior to engaging in such activities with these countries. Please be sure and contact the Export Control Compliance Program before you consider involvement in any such activity.
Atomic Energy Act (AEA) Data – Tiers (1-3)
The Atomic Energy Act (AEA) was established in 1946 after World War II in order to determine how the United States would control and manage nuclear technology and to assure the proper management of source, special nuclear, and byproduct material. The National Nuclear Security Administration (NNSA) is the agency within the Department of Energy that is responsible for administering regulations controlling a broad range of atomic energy activities, including assistance to foreign atomic energy activities related to nuclear weapons, and AEA-controlled information, which includes all classified or unclassified policies, practices, information, technical data, items, materials, facilities, equipment, software, technologies or services used to design, assess, detect, develop, fabricate, qualify, maintain, transport, render safe, or dispose of devices implementing a military application of atomic energy. These span the range of Technology Readiness Levels from basic research through Manufacturing Readiness Levels (expanding scientific principles that may have manufacturing implications through production).
Indications of AEA control may include information which is developed utilizing nuclear weapon program funding. Under NNSA Policy NAP 476.1, AEA-controlled information is managed in a graded manner:
- Tier 1: Tier 1 contains everything that involves the unique category of Restricted Data (RD) or Formerly Restricted Data (FRD). Restricted Data is all data concerning the design, manufacture or utilization of atomic weapons; production of special nuclear material; or use of special nuclear material. Formerly restricted data is classified information that has been removed from the RD category, which relates to military utilization of atomic weapons and which needs specific safeguarding. Note, the word “formerly restricted” does not mean unclassified; all Restricted Data and Formerly Restricted Data is classified. Because the University of Nebraska is not accredited to handle or store classified materials, UNL personnel cannot engage in research or other work involving Tier 1 data.
- Tier 2: Tier 2 applies to non-nuclear parts of atomic weapons or the utilization of facilities whose disclosure would contribute significantly to another nation’s atomic weapon capability. Tier 2 contains data that is not Restricted Data or Formerly Restricted Data, but which reveals a specific nuclear weapon function (e.g. arming or fusing) or reveals special capabilities necessary to design, develop, produce or evaluate nuclear weapons or nuclear weapon tests or any other nuclear explosions. Data controlled under Tier 2 may be classified or unclassified. Some information and items, which if used for other purposes would be identified in the nuclear equipment and material listed in the Commerce control list (10 CFR 110), the U.S. Munitions List (22 CFR 121), Unclassified Controlled Nuclear Information (DOE Order 241.1B), or DOE Official Use Only, are considered Tier 2 when incorporated in, modified for, or manufactured for nuclear weapon-related activities. Because the University of Nebraska is not accredited to handle or store classified materials, UNL personnel cannot engage in research or other work involving classified Tier 2 data.
- Tier 3: Tier 3 contains all information and items used in nuclear weapon-related activities which are neither Tier 1 nor Tier 2.
UNL faculty and staff conducting work regulated under the AEA Tier 2 or Tier 3 must have a Technology Control Plan (TCP) in place before the project starts. Due to the restrictions on this type of work, AEA regulated projects are treated similarly to work falling under the International Traffic in Arms Regulations. Please contact the Export Compliance Program, to ensure all appropriate approvals are in place and a TCP has been established prior to beginning the project.
See Regulatory Information & Other Resources for additional travel requirements when engaging in DOE work that is regulated under the AEA. Restrictions and requirements are typically included in award documents, but please contact the Export Compliance Program with questions about how this might apply to your work under a DOE award.
Commerce Control List (CCL), ECCNs, & EAR 99
A key in determining whether an export license is needed or applicable in controlling a particular item, from the Department of Commerce, is knowing whether the item you intend to export has a specific Export Control Classification Number (ECCN). The ECCN is an alpha-numeric code, (which may look something like this: 3A001) and that describes the item and indicates licensing requirements. All ECCNs are listed in the Commerce Control List (CCL) (Supplement No. 1 to Part 774 of the EAR) which is available on the Government Printing Office website. The CCL is divided into the following ten broad categories, and each category is further subdivided into five product groups.
| 0 | Nuclear & Miscellaneous |
| 1 | Materials, Chemicals, Microorganisms and Toxins |
| 2 | Materials Processing |
| 3 | Electronics |
| 4 | Computers |
| 5 Part 1 | Telecommunications |
| 5 Part 2 | Information Security |
| 6 | Sensors and Lasers |
| 7 | Navigation and Avionics |
| 8 | Marine |
| 9 | Aerospace and Propulsion |
| A | Systems, Equipment and Components |
| B | Test, Inspection and Production Equipment |
| C | Material |
| D | Software |
| E | Technology |
If your item falls under U.S. Department of Commerce jurisdiction but is not listed on the CCL, it is designated as EAR99.
EAR99 is the general “catch-all” classification number assigned to any item that is subject to the EAR but that does not have a specific export control classification number listed in the Commerce Control list. EAR99 items generally consist of low-technology consumer goods and do not require a license in many situations. However, if you plan to export an EAR99 item to an embargoed country, to an end-user of concern, or in support of a prohibited end-use, you may be required to obtain a license and should check with ECCP staff prior to making any export decisions.
Controlled Unclassified Information (CUI) & Covered Defense Information (CDI)
This information is intended to provide guidance to the UNL campus regarding applicability of Controlled Unclassified Information (CUI) and Covered Defense Information (CDI) in research and securing controlled information via Office 365 US Government.
Controlled Unclassified Information (CUI) is federal non-classified information (32 CFR Part 2002) the U.S. Government creates or possesses, or that a non-federal entity (i.e. the University of Nebraska-Lincoln) receives, possesses, or creates for, or on behalf of, the U.S Government, that requires information security controls to safeguard or disseminate.
Covered Defense Information (CDI) is a category of CUI. CDI is a specific term used by the DoD to describe information that requires protection under the DFARS Clause 252.204-7012, it is defined as:
- Controlled Technical Information (CTI)
- DoD Critical Infrastructure Security Information
- Naval Nuclear Propulsion Information
- Unclassified Controlled Nuclear Information (UCNI) – Defense
As described in the Controlled Unclassified Information (CUI) Registry, CUI is divided into the following organizational groups:
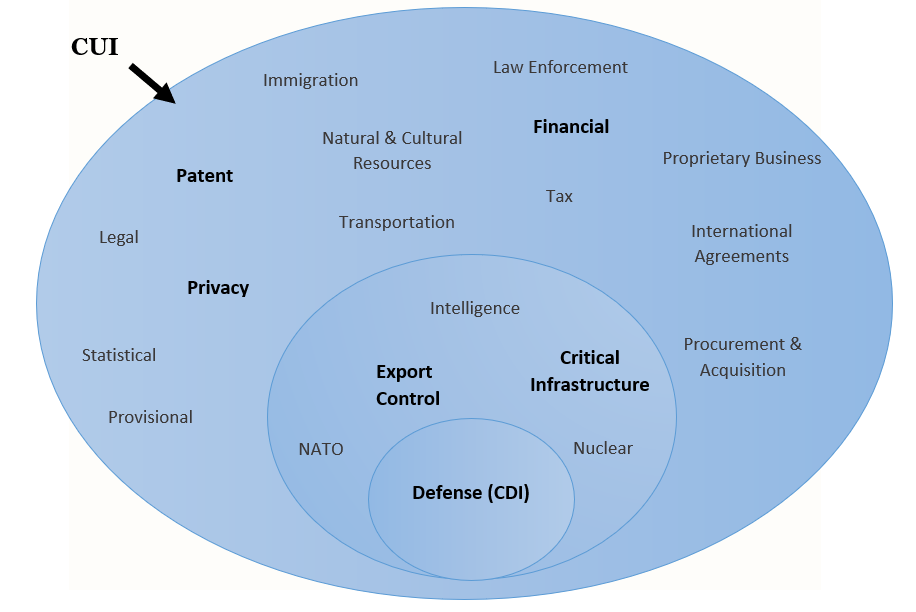
- The categories in bold are examples of data that university researchers and administrators may commonly encounter in the course of their work. For a full list of subgroups within each organizational group, reference the National Archives.
- All CUI requires some form of safeguarding however, some groups of CUI must also comply with export control regulations to protect the information; these will most commonly fall under the categories listed in the two inner circles.
Key Information:
- While CUI encompasses multiple areas of information, University researchers will typically encounter CUI requirements included in sponsor contracts (FAR/DFAR (252.204-7008, 7009, 7012 clauses) or in regulations governing the type of data they are receiving/collecting/storing/transmitting (e.g. HIPAA, FERPA, genetic information).
- Information, as defined by the federal CUI Program, may include research data and other project information that a research team receives, possesses, or creates in the performance of a sponsored contract.
- This means that a research project at the University of Nebraska-Lincoln (UNL) may require the implementation of information security controls when the federal contract/award contains language/clauses (FAR, DFAR) requiring those controls for CUI or CDI.
- The Office of Research Compliance, Integrity, and Security (RCIS) and Office of Sponsored Programs (OSP) review research contracts and awards to determine the applicability of the clauses in negotiation with the sponsor.
- A research project may also include CUI if it is using data acquired under a Data Use/Transfer Agreement (DUA/DTA) and the data (e.g. CDI/HIPAA/PHI) is categorized as CUI.
For Marking of CUI and other helpful information
The table below has questions that are intended to help research personnel determine if something is Controlled Unclassified Information (CUI) and how to document/treat it. This is a helpful guide but does not include all of the needed information. For additional resources please use the following links below:
The CUI Marking Handbook gives you instructions on how to handle and document CUI as well as other helpful information. The DoD Instruction 5200.48 Controlled Unclassified Information (CUI) has information about CUI regulations regarding DoD.
University of Nebraska-Lincoln Guidance Document for Marking Research Documents and Presentations to ensure appropriate access and documentation.
Please use the table below while creating presentations, documents, reports that may be using controlled unclassified and proprietary information.
*Documents, reports, etc. will be referred to as article in the guidance*
| Question | Yes | No | |
| 1. | Does the article include any controlled or proprietary information? | Identify what type of controlled and/or proprietary information it includes, including what the relevant sources are and go to Question 2. | No marking necessary. (If an article does not include any type of controlled and/or proprietary information, it may be useful to mark the first page as such). |
| 2. | Did the external party provide you information that is proprietary and non-public that you have included in the article? (Make sure to check that the external party allows such information to be included by reviewing all necessary forms/documents, non-disclosure agreements, material transfer agreements and any other documents). | Ensure that the cover page is marked with the inclusion of such information and consider question 4. | No action required. |
| 3. | Does the article include any research results subject to a publication or dissemination restriction? An example is the DFAR 252.204-7000 Disclosure of Information clause. | Consider question 4. | No marking necessary. (If an article does not include any type of controlled and/or proprietary information, it may be useful to mark the first page as such). |
| 4. | Considering the type of controlled information identified by questions 2 and 3, is the controlled information technical information subject to the US export control regulations? (Consider this information. Technology, under the EAR and Technical Data under the ITAR.) | If yes, mark the cover page with the Export Control disclaimer. (Below guidance) Best Practice: consider including in the portion markers in the relevant sections of the document the classification and jurisdiction of the technology or technical data. (ITAR Cat II or ECCN EAR99). Consider Question 5. | No additional action required. |
| 5. | Considering the type of controlled information identified in earlier questions, is there any Controlled Unclassified Information included? | Mark in accordance with CUI Marking Handbook At a minimum, ensure that the Cover page is marked Controlled or CUI and that each page in the document includes a Banner marking of Controlled or CUI. If CUI specified, you must include the specific authority in the banner marking. (E.g. Export Controlled Research should be marked as CUI//SP-EXPTR Best Practice: if the document includes both controlled and publicly releasable information, consider portion marking. [1] | No additional action required. |
| 6. | Considering the type of controlled information identified in earlier questions, is there any Covered Defense Information included? | Mark in accordance with the DoD Instruction 5200.48 Controlled Unclassified Information (CUI) | No additional action required. |
The following disclaimer language is provided as a template for research personnel to utilize:
Export Control Disclaimer – WARNING – This document contains technical data whose export is restricted by the Arms Export Control Act (Title 22, U.S.C., Sec 2751, et seq.) or the Export Administration Act of 1979, as amended (Title 50, U.S.C., App. 2401 et seq.). Violations of these export laws are subject to severe criminal penalties.
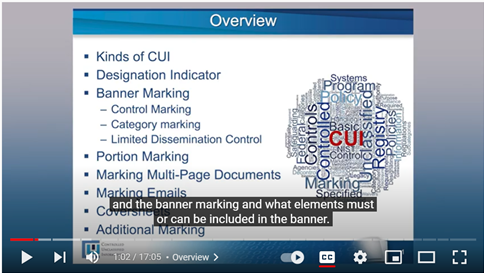
Video Reference for CUI-Marking Instructions
Video: Introduction to Marking CUI (updated August 6, 2018) – For an overview of how to mark documents, emails, presentations, systems, and other files containing CUI, watch this video. It addresses the designation indicator and CUI banner marking, including CUI control marking, CUI category markings, and Limited Dissemination Control Markings. The video also discusses portion marking, cover sheets, marking multipage documents, and decontrolling CUI.
- 0:00 — Intro: What a Marking Standard Is
- 1:32 — CUI Basics
- 1:44 — CUI-Specified
- 2:38 — Designation Indicator
- 3:22 — Banner Marking
- 6:48 — Limited Dissemination Controls
- 8:15 — Portion Marking
- 9:31 — Marking Multiple Pages
- 9:53 — Separate Banner Markings from Administrative Markings
- 10:49 — Coversheets
- 11:32 — Forms
- 12:17 — Email
- 13:20 — Presentations/PowerPoints
- 13:53 — Transmittal Documents
- 14:28 — Electronic Media (hard drive, USB, CD ,etc.)
- 14:56 — Audio, Video, and Photographs
- 15:40 — Shipping and Mailing
- 16:04 — Decontrol CU
See the video for details:
For more videos from the National Archive on CUI related topics please use the link below:
CUI Training | National Archives
See also guidance topic on Safeguarding Covered Defense Information, Controlled Unclassified Information & Office 365 US Government.
Training Resources
If you will be working with CUI, Export Control Compliance Staff may require you to take a course on CUI. If you score a 70% or better you will pass the course and receive a certification. This certification does not expire, however UNL has determined it will be valid for 3 years upon the completion date.
If Export Control requires you to complete a CUI training, use the link below for access to the training and information. (Please note, if you are not required to take this training you are still allowed to take the training for your own personal knowledge).
DoD Mandatory Controlled Unclassified Information (CUI) Training (usalearning.gov)
For additional resources regarding CUI and Cyber Security Training please use the following resources below.
- CUI information Brochure/Handout.
- DoD Cyber Awareness Challenge, this training covers several different areas of Cyber Awareness.
- Identifying and Safeguarding Personally Identifiable Information (PII), this training discusses how to correctly identify and safeguard PII.
For further assistance/questions please consult with UNL Export Control Compliance Personnel. *If your project is documented as an Export Control Project in NuRamp, there may be more information that is specific to your research in the Project details.*
Critical and Emerging Technology
Critical and Emerging Technologies reference broader areas of technology the U.S. government has identified as having an economic and/or strategic defense advantage and are taking measures to control the proliferation of these technologies.
The areas below are a few of the common areas of potential national security for Critical and Emerging Technologies. There are more areas that may be considered Critical and Emerging, and this list is subject to change depending on the federal government.
If you are planning on or are conducting research, work or any other activities in these fields, then your work may fall under the new Critical and Emerging Technology policy (Listed Update) issued under the National Science and Technology Council (NSTC) dated February 2024.
To help determine if your activities are subject to the new policy please see the questions below. The questions below are not comprehensive but are meant to give guidance. UNL Export Control also has additional information to help you determine if you work may be export controlled. If you have questions or think your work may relate to this policy, please contact UNL Export Control.
- Does your sponsor (RFI/RFP, award contract, grant, or other documents) state that the work is Critical and Emerging or include other Research Security, Cybersecurity, or Export Control restrictions/clauses?
- Regardless of funding, are you planning or are you working with international collaborators?
- Including sending equipment, material or data internationally?
- Is your work controlled under the EAR, NRC, ITAR or another regulatory agency?
If you answered yes to any of the items above, your work may be controlled under this policy.
Common areas defined as Critical and Emerging technologies for national security can include:
- Advanced Computing: Using computer clusters or supercomputers to complete projects, research or activities.
- Advanced Engineering Materials: Material specially designed for specific applications that has improved properties compared to traditional materials.
- Advanced Gas Turbine Engine Technologies: Engines or technologies to improve standard Advanced Gas Turbine Engines.
- Advanced and Networked Sensing and Signature Management: Process of understanding, studying and modifying electromagnetic signatures, commonly done in military applications.
- Advanced Manufacturing: New and advanced equipment, technologies and procedures to improve manufacturing of products.
- Artificial Intelligence: Theory and development of computer systems in order to perform specific tasks or tasks that involve intelligence.
- Biotechnologies: The use of living organisms or biological material/systems to create or modify other products.
- Clean Energy Generation and Storage: The process of creating clean power solutions, storage and products.
- Data Privacy, Data Security, and Cybersecurity Technologies: Data that may have specific safety, security, national threat and other controlled data and cybersecurity technologies, data, and products.
- Directed Energy: Using electromagnetic systems to alter chemical and electrical energy into radiated energy that can be used to target a specific area.
- Highly Automated, Autonomous, and Uncrewed Systems (UxS), and Robotics: Devices and equipment involving or using Uncrewed Systems and Robotics.
- Human-Machine Interfaces: Devices that allow for the interaction of human and machines, systems or devices.
- Hypersonics: Equipment, materials, or devices capable of going five times faster than the speed of sound (Mach 5).
- Integrated Communication and Networking Technologies: The use of equipment, devices or software to create different communication or networking groups that can process and communicate information.
- Positioning, Navigation, and Timing (PNT) Technologies: Technology used to determine how, where and when something may happen.
- Quantum Information and Enabling Technologies: The use of quantum mechanics and theory to process and transmit information.
- Semiconductors and Microelectronics: Semiconductors or integrated circuits are made of solid substances that are made up of conductive and insulator material for electronic devices. Microelectronics are small scale circuits or devices.
- Space Technologies and Systems: Equipment, devices, software and material that is used for space related activities.
Advanced Computing and Semiconductor Research and Manufacturing
New Export Controls Related to Advanced Computing and Semiconductor Manufacturing
On October 7, 2022, the Department of Commerce announced a series of new export controls rules on advanced computing and semiconductor manufacturing items. The interim final rules were made effective on 11/17/2023. The regulatory agencies’ guidance are subject to change, so please make sure to contact UNL Export Control for the most current regulations. While the new export control regulations are largely targeted at the People’s Republic of China, including Hong Kong, (collectively “PRC”), the breadth and scope extend beyond the PRC to Macau and other D5 Countries. The controls are intended to restrict the PRC’s ability to obtain advanced computing chips, develop and maintain supercomputers, and manufacture advanced semiconductors. In addition, the new rules make clear that foreign government actions that prevent the U.S. from making compliance determinations will impact certain foreign companies’ access to U.S. technology.
Per UNL ECCP Policy 9.001, all international shipments must be approved by UNL Export Control Compliance Personnel (ECCP). If you work with advanced computing chips, supercomputers, semiconductors, or integrated circuits, please make sure to contact UNL ECCP if you plan on working with foreign nationals in the US or will be working with foreign nationals or entities outside the US.
Key Information:
- Adds certain advanced and high-performance computing chips and computer commodities that contain such chips to the Commerce Control List (CCL) – meaning an Export Control license will likely be required.
- There are new requirements for export control licenses based on the following items. The following items are likely prohibited without an export license (please check with UNL Export Control Compliance Personnel (ECCP)):
- Supercomputer, semiconductor, integrated circuits or semiconductor manufacturing equipment being sent to or used in the PRC, Macau or any D5 country.
- If any of the items are sent to or will be used in the PRC, Macau or any D5 country.
- If you have material or manufacturing equipment developed by an entity headquartered in, located in or having the parent company headquartered in the PRC, Macau or any D5 country.
- If you know your export, reexport or transfer of the items listed above will be used for activities specified in 744.6(c)(2)(i) through 744.6(c)(2)(iii).
- If you know an item is destined to a semiconductor fabrication facility (any place where production occurs) in the PRC, Macau or any D5 country that fabricates integrated circuits. Licenses for facilities owned by PRC entities will face a “presumption of denial”, and facilities owned by multinationals will be decided on a case-by-case basis.
- Any form of “Support” from a U.S. person or entity that contributes to the development and/or production of integrated circuits at certain PRC-located semiconductor fabrication facilities without an export control license. Fundamental Research or Fundamental Research Exclusion (FRE) does not remove the need for an export license for “Support”.
- Reviews Research Personnel Activities (Services and/or Development) at Advanced NODE Facilities in PRC, of other facilities working with PRC under the Foreign Direct Product Rule (FDPR).
- In addition, no license exceptions (including for temporary travel) will be available for certain integrated circuits and other items described in this new rule (including associated software and technology) when destined to the PRC.
- Shipping, transmitting, or transferring to or within the PRC; facilitating the shipment, transmission, or transfer to or within the PRC; or servicing (anywhere), any item that you know will be used in the development or production of integrated circuits at a semiconductor fabrication facility located in the PRC that fabricates Advanced-Node Integrated Circuits meeting any of the following criteria:
- Logic integrated circuits using a non-planar architecture or with a “production” technology node of 16/14 nanometers or less,
- NOT-AND (NAND) memory integrated circuits with 128 layers or more; or
- Dynamic random-access memory (DRAM) integrated circuits using a “production” technology node of 18 nanometer half-pitch or less.
*If you are unsure if any of the requirements above will be met, please contact UNL ECCP.
- Shipping, transmitting, or transferring to or within the PRC any item; facilitating the shipment, transmission, or transfer to or within the PRC of any item; or servicing any item located in the PRC, that you know will be used in the development or production of integrated circuits at any semiconductor fabrication facility located in the PRC, regardless of end user.
- Exporting any item when you have knowledge that the item will be used in the development, production, use, operation, installation, maintenance, repair, overhaul, or refurbishing of a “supercomputer” located in or destined to the PRC.
- Exporting any item when you have knowledge that the item will be incorporated into, or used in the development, or production, of any component or equipment that will be used in a “supercomputer” located in or destined to the PRC.
- Exporting any item when you have knowledge that the item will be used in the development or production in the PRC of any parts, components, or equipment as follows: equipment for the manufacturing of semiconductor devices or materials; test equipment for testing finished or unfinished semiconductor devices; test, inspection and production commodities for military electronics; other equipment for the manufacture of electronics parts, components, and materials; or other equipment for the inspection or testing of electronic components and materials.
*No license exceptions are available for the activities above
*There is a presumption of denial for any license applications made for the activities above
*The regulations are subject to change, please make sure to contact UNL ECCP if you have any questions or may be working in any of the areas above. The items above are a general overview of the new regulations, but do not incorporate the full regulation. Please review the full regulation here or contact UNL ECCP.
In addition, many entities in the PRC (including universities) are being added on a rolling basis to restricted parties’ lists administered by Federal Regulatory agencies such as the Department of Commerce. As a result, heightened due diligence is necessary when dealing with parties in the PRC. Contact the UNL ECCP for restricted party screening (RPS) of foreign entities or individuals that you wish to collaborate or otherwise engage in research activities with.
Some common items controlled and regulated under these guidelines include the following. This is just an example and does not include all regulated items. The technology controlled under these ECCNs is subject to licensing requirements depending on the end use and country controls and other controls. Please reach out to UNL ECCP for the most up to date guidance.
| Export Control Classification Number (ECC) | Description of Semiconductor Manufacturing Equipment (SME) |
| 3A090.a | Integrated circuits having one or more digital processing units having either of the following: a.1. a ‘total processing performance’ of 4800 or more, or a.2. a ‘total processing performance’ of 1600 or more and a ‘performance density’ of 5.92 or more. |
| 3A090.b | Integrated circuits having one or more digital processing units having either of the following: b.1. a ‘total processing performance’ of 2400 or more and less than 4800 and a ‘performance density’ of 1.6 or more and less than 5.92, or b.2. a ‘total processing performance’ of 1600 or more and a ‘performance density’ of 3.2 or more and less than 5.92. |
| 3B001.a.4 | Equip. designed for silicon (Si), carbon doped silicon, silicon germanium (SiGe), or carbon doped SiGe epitaxial growth |
| 3B001.d | Deposition equipment |
| 3B001.f | Lithography equipment |
| 3B001.j | “EUV” mask substrates |
| 3B001.k | Equipment designed for ion beam deposition or physical vapor deposition of multilayer reflector for “EUV” masks |
| 3B001.l | “EUV” pellicles. |
| 3B001.m | Equipment for manufacturing “EUV” pellicles. |
| 3B001.n | Equipment designed for coating, depositing, baking, or developing photoresist formulated for “EUV” lithography. |
| 3B001.o | Semiconductor wafer fabrication annealing equipment with specified parameters. |
| 3B001.p | Three types of semiconductor wafer fabrication cleaning and removal equipment |
| 3B002.c | Inspection equipment designed for “EUV” mask blanks or “EUV” patterned masks. |
Artificial Intelligence
There are many types of Artificial Intelligence (AI), which are based on its capabilities, functionalities and technology. While these types of AI are different and have different capabilities, there are no specifications on which type of AI may be more closely regulated under emerging technology regulations. Instead, the controls are likely to come from what the AI is created for, what it can be used for and the type of equipment that is used.
Based on the latest word from Bureau of Industry and Security, they are writing regulations to control certain artificial intelligence related technology and products. It is important to keep that in mind that with the evolving regulatory environment even if you’ve never dealt with or had to think about export controls before, you may end up needing to work with UNL ECCP in the future to ensure compliance with any federal regulations. As of right now there are some regulated AI which pertains to AI and related equipment with military application which meets certain USML categories criteria, particularly category VIII, XII and XIII.
Capabilities
- Narrow/Weak AI
- This type of AI can perform specific tasks, such as playing games, navigation, internet searches. This type of AI operates under very specific contexts.
- General/Strong AI
- This type of AI can complete more than specific tasks, and can function on its own with its own cognitive capacity.
- Superintelligent AI
- This type of AI is still in the development stage, however, the concept would be AI that is capable of surpassing human intelligence.
Functionality
- Reactive Machines
- These AI systems do not store memory or past experiences, and they react to the situation in the moment.
- Limited Memory
- Unlike Reactive Machines, Limited Memory does use past data to make informed decisions. This is the most common for AI systems.
- Theory of Mind
- Theory of Mind AI is an improvement on Limited Memory AI as it uses not only past data, but also human emotions, needs, and other human activities/needs.
- Self-aware AI
- As with Superintelligent AI, this is theoretical. The over all idea of this type of AI would be that the AI would not only be able to understand human emotions, process and learn data but would also become self-aware/sentient.
Technology
- Machine Learning (ML) (one of the main branches)
- AI systems capable of self-improvement and learning through experience. Original software/code is created, and improves upon itself through its experiences.
- New ECCN 2B001 is related to Machine Learning Technology (see more below in ECCNS).
- Deep Learning (one of the main branches)
- Deep Learning is a subset of Machine Learning, the difference is that it learns from large amounts of data versus from experience. This type of AI is used in many image recognition and voice controlled consumer devices.
- Natural Language Processing (one of the main branches)
- This AI is used for interpreting human language and is common for chatbots and translation services/analysis.
- Robotics (one of the main branches)
- This category covers robots and computers that are designed to use or work with AI.
- Computer Vision
- Computer Vision uses AI to interpret the world visually for different type of image analysis and surveillance.
- Expert Systems
- This system is used to answer questions or solve problems under a specific category or set of rules.
Below are a few examples of how AI may be regulated:
- In July 2020 the Bureau of Industry and Security issued a Notice of Inquiry on Advanced Surveillance Systems and Other Items of Human Rights Concerns and proposed amendments to that in their proposed rule that was issued 07/29/2024 Export Administration Regulations: Crime Controls and Expansion/Update of U.S. Persons Controls.
- There will likely be new licensing requirements for human facial recognition software and other biometric systems for surveillance some of which incorporate artificial intelligence as well as changes to end user/end country controls
- If you create Source Code for AI software or algorithms, these may be controlled under the EAR or USML regulations and have restrictions on publication or sharing of source code. The regulations may also restrict the sharing of source code to collaborators or developing source code with foreign collaborators.
- Data Transfer Use Agreements or other federal licenses may be required to share source code with others.
- Additional Reading materials on AI can be found below:
Please reach out to UNL ECCP for the latest guidance.
Hypersonics
Hypersonics research involves working with material, equipment and items that can travel or are used to travel over five times the speed of sound. Hypersonics were first used during World War 2 and have been continuing to improve in their use for military application, commercial application and in the private sectors. As Hypersonics can be used for a wide variety of reasons, research, data and equipment around Hypersonics may be subject to the International Traffic and Arms Regulation (ITAR) for use in military applications. Hypersonics may also be subject to the Export Administration Regulation (EAR) for items, data and equipment that are dual use (civilian and military).
On October 7th, 2022 the Bureau of Industry and Security (BIS) released the interim final rule (IFR) “Implementation of Additional Export Controls: Certain Advanced Computing and Semiconductor Manufacturing Items; Supercomputer and Semiconductor End Use; Entity List Modification”. The rule was in part a strategic effort to disrupt China’s ability to use advanced computers for its military modernization efforts including their development of weapons of mass destruction such as nuclear and hypersonic weapons.
International collaboration pertaining to hypersonic may warrant additional safeguarding to prevent violation of federal regulations due to the potential military and dual use application. Whether the data, equipment or items are controlled under the ITAR or EAR, a license may be required to work with international collaborations. This is detailed in the Oct. 7th rule relating to US persons activity controls, which creates restrictions on foreign end uses and end users of concern.
Determination of if a license is required will be done by the export control office. Please reach out to them if you want to or are planning to work with a foreign entity or individual. This includes working on publications, sending parts, data, equipment, applying for grants, providing a service and more. The determination will be made based on the regulations, type of work, and countries involved in the research. Countries such as Cuba, Iran, North Korea, Syria, Sudan, Russia and China have more restrictions and in some cases are sanctioned from doing work related to hypersonics with the US.
Quantum Information and Enabling Technologies
The Critical and Emerging technologies policy splits Quantum Information and Enabling Technologies into five sections. These five sections are all based on quantum mechanics and quantum theory.
- Quantum computing
- Involves a multidisciplinary approach to solve complex problems using quantum mechanics/theory.
- Materials, isotopes, and fabrication techniques for quantum devices
- Research involving quantum devices, quantum materials, or other materials/items/data that could be used to create or improve quantum devices, techniques, technologies, and overall quantum related items.
- Not limited to semiconductors, computer devices or programs/software.
- If the material, isotopes, technique or device is capable of quantum research, there may be controls around how that system may be used based on the regulations.
- Research involving quantum devices, quantum materials, or other materials/items/data that could be used to create or improve quantum devices, techniques, technologies, and overall quantum related items.
- Quantum sensing
- Using quantum systems to make extremely accurate measurements in the environment and our surroundings.
- Quantum communications and networking
- Sending of qubits between quantum networks/processers.
- Ways of communicating through optical fibers, copper wire or microwaves in order to provide faster and more reliable networks.
- Supporting systems
- Systems that are capable of quantum mechanics and quantum theory either in principle or practice.
- If a system is capable of quantum research, there may be controls around how that system may be used based on the regulations.
- Systems that are capable of quantum mechanics and quantum theory either in principle or practice.
Like other emerging technology areas, regulations are coming out that control certain equipment, and or end use, and may require additional safeguarding if research will be done in a foreign country, for a foreign sponsor or with international collaborators.
In addition to the critical and emerging regulations, a new rule was issued on 9/6/2024 which added new ECCNS, restrictions on collaborations, international shipping and working with foreign nationals (including foreign nationals inside the US (Deemed Export)).
Some common items controlled and regulated under these guidelines include the following. This is just an example and does not include all regulated items. The technology controlled under these ECCNs is subject to licensing requirements depending on the end use and country controls and other controls. Please reach out to UNL ECCP for the most up to date guidance.
| Export Control Classification Number (ECC) | Description of Quantum Technologies |
| 3A901* | Quantum processors based on superconducting arrays must operate at extremely low temperatures (20 mK or below), and other quantum computing implementations require colling below 200 mK. |
| 3A904* | Cryogenic cooling systems and components. |
| 3B904* | Cryogenic wafer probing equipment. |
| 3C907* | Epitaxial materials consisting of a “substrate” having at least one epitaxially grown layer and containing other specified materials. |
| 3C908* | Fluorides, hydrides, chlorides, of silicon or germanium, containing other specified materials. |
| 3C909* | Silicon, silicon oxides, germanium or germanium oxides, containing any other specified materials. |
| 3D901* | “Software”, not specified elsewhere, “specially designed” or modified for the “development,” “production,” of items controlled in ECCN 3A901.b, 3B903, or 3B904. |
| 3E003 | silicon-on insulation (SOI) technology for the “development” or “production” related to radiation hardening of integrated circuits. “Technology” for the development or production of quantum technology |
| 3E003.b | Hetero-structure semiconductor electronic devices such as high electron mobility transistors (HEMT), hetero-bipolar transistors (HBT), quantum well and super lattice devices; Note: 3E003.b does not control “technology” for high electron mobility transistors (HEMT) operating at frequencies lower than 31.8 GHz and hetero-junction bipolar transistors (HBT) operating at frequencies lower than 31.8 GHz. |
| 3E901* | “Technology” according to the General Technology Note for the “development” or “production” of items controlled by 3A901, 3A904, 3B903, 3B904, 3C907, 3C908, or 3C909. |
| 4A006** | Quantum computers and related electronic assemblies and components including specified qubit devices and circuits and quantum control components and measurement devices |
| 4A906* | Quantum computers and related “electronic assemblies” and “components” therefor. |
| 4D001 | a. “Software” “specially designed” or modified for the “development” or “production”, of equipment or “software” controlled by 4A001, 4A003, 4A004, 4A005 or 4D (except 4D090, 4D980, 4D993 or 4D994). b. “Software”, other than that controlled by 4D001.a, “specially designed” or modified for the “development” or “production” of equipment as follows: b.1. “Digital computers” having an “Adjusted Peak Performance” (“APP”) exceeding 24 Weighted TeraFLOPS (WT); b.2. “Electronic assemblies” “specially designed” or modified for enhancing performance by aggregation of processors so that the “APP” of the aggregation exceeds the limit in 4D001.b.1. |
| 4D906* | “Software” “specially designed” or modified for the “development” or “production”, of commodities controlled by 4A906.b or 4A906.c. |
| 4E001 | a. “Technology” according to the General Technology Note, for the “development”, “production”, or “use” of equipment or “software” controlled by 4A (except 4A980 or 4A994 and “use” of equipment controlled under 4A090) or 4D (except 4D980, 4D993, 4D994 and “use” of software controlled under 4D090). b. “Technology” according to the General Technology Note, other than that controlled by 4E001.a, for the “development” or “production” of equipment as follows: b.1. “Digital computers” having an “Adjusted Peak Performance” (“APP”) exceeding 24 Weighted TeraFLOPS (WT); b.2. “Electronic assemblies” “specially designed” or modified for enhancing performance by aggregation of processors so that the “APP” of the aggregation exceeds the limit in 4E001.b.1. c. “Technology” for the “development” of “intrusion software.” Note 1: 4E001.a and 4E001.c do not apply to “vulnerability disclosure” or “cyber incident response”. Note 2: Note 1 does not diminish national authorities’ rights to ascertain compliance with 4E001.a and 4E001.c. |
| 4E906* | “technology” for the “development” or “production” of items controlled by 4A906.b, 4A906.c, or 4D906; and to control in 4E906.b “technology” for the “use” of “software” controlled by 4D906. |
| 5A002 | “Information security” systems, equipment and “components,” |
| 6A996 | “Magnetometers” not controlled by ECCN 6A006, “Superconductive” electromagnetic sensors, and “specially designed” “components” |
*ECCN’s have been added under new rule 9/6/2024 as quantum items.
** ECCN has been proposed as a new ECCN by BIS, but has not been finalized, this ECCN may be approved in the future, as an ECCN to categorize specific quantum related devices*
Additional Resources and Considerations
Facial Recognition Systems have not been identified as Critical and Emerging Technology, but some of the software, technology, equipment and techniques have been controlled by other Critical and Emerging Technology regulations as well as some specific regulations identified in Advanced Surveillance Systems and Other Items of Human Rights Concern Notice of Inquiry (NOI), which was published July 17th, 2020.
The BIS introduced a new rule on 9/6/2024 titled “Commerce Control List Additions and Revisions; Implementation of Controls on Advanced Technologies Consistent with Control Implemented by International Partners”. This rule discusses the addition of ECCNS and license requirements for advanced technologies and quantum devices. The new regulation has added 11 new ECCNS, and has created additional license requirements for countries listed as group D and E, as well as country group A. For country group A, certain countries have adopted United States Export Control Policies and may be exempt from licensing requirements (License Exception IEC Eligible). Lastly, this rule adds restrictions on deemed export for certain technologies and software related to advanced computing and quantum technology.
If you are working within any of the fields listed above that are categorized as critical and emerging technologies, please contact UNL Export Control before shipping, sharing, collaborating or any other form of research/work with a foreign entity/institution or individual. There may be restrictions upon the type of work that can be conducted in the United States with foreign nationals depending on contractual agreement, categorization (EAR/ITAR) and deemed export regulations.
An additional regulation to be aware of is the Foreign-Security End User (FSEU), which restricts shipping and collaboration with FSEU. FSEU’s can be defined as armed forces, police, intelligence, or other internal security forces that are a part of or belong to countries listed in Groups D:5 and E.
These regulations must be followed no matter if the research is funded or unfunded, and if the research will be published or is already published. These regulations are constantly growing, so please reach out for any questions or concerns around critical and emerging technology.
Additional ECCNS and information that have resulted in changes in how technology is controlled. Some of the ECCNS relate directly to the items listed above as Critical and Emerging technologies while others relate to similar fields of research.
| Final Rule | ECCN | ECCN Definition | Additional Notes |
| 1/06/2020 | 0Y521 | Series Supplement—Extension of Controls on an Emerging Technology (Software Specially Designed To Automate the Analysis of Geospatial Imagery Classification) | |
| 12/8/2023 | 2B001 | Machine tools and any combination thereof, for removing (or cutting) metals, ceramics or “composites”, which, according to the manufacturer’s technical specifications, can be equipped with electronic devices for “numerical control”; as follows (see List of Items Controlled). | |
| 9/6/2024 | 2B910 | Additive manufacturing equipment, designed to produce metal or metal alloy components. | Controlled as specially designed for military material and equipment. |
| 5/23/2019 | 3A001.b | Electronic Items | ECCN 3A001 is amended by adding paragraph b.3.f to control discrete microwave transistors ‘‘rated for operation with a peak saturated power output greater than 5 W (37.0 dBm) at all frequencies exceeding 8.5 GHz up to and including 31.8 GHz’’. |
| 7/17/2020 | 3A980 | Voice print identification systems and components | |
| 7/17/2020 | 3A981 | Polygraphs and psychological stress analysis equipment and components | |
| 9/6/2024 | 3B903 | Scanning Electron Microscope (SEM) equipment designed for imaging semiconductor devices or integrated circuits | A specialized SEM can be used to reverse engineer integrated circuits and perform chip design recovery and for this reason warrants national security controls to protect innovation in integrated circuit development of the United States and other supplier countries. |
| 11/17/2023 | 3D003 | ‘Computational lithography’ “software” “specially designed” for the “development” of patterns on “EUV”- lithography masks or reticles. | |
| 10/5/2020 | 3E004 | ‘Technology’’ ‘‘Required’’ for the Slicing, Grinding and Polishing of 300 mm Diameter Silicon Wafers To Achieve a ‘Site Front Least sQuares Range’ (‘SFQR’) Less Than or Equal to 20 nm at Any Site of 26 mm x 8 mm on the Front Surface of the Wafer and an Edge Exclusion Less Than or Equal to 2 mm | This rule adds ECCN 3E004 to control ‘‘technology’’ for the production of substrates for high-end integrated circuits. The parameters include minimization of the flatness and the surface defect. |
| 5/23/2019 | 5A002 | Information Security | ECCN 5A002 is amended in order to add a control on certain types of postquantum cryptographic algorithms. |
| 10/5/2020 | 5A004.b, 5D002, 5E002 | Systems, Software, Technology | These ECCNS relate to Digital Forensic and cyber incident tools, equipment and software |
| 10/5/2020 | 5D001.e and 5E001.a | Software and Technology | Surveillance equipment and software |
| 5/23/2019 | 9A004 | Space Launch Vehicles and ‘‘Spacecraft’’, ‘‘Spacecraft Buses’’, ‘‘Spacecraft Payloads’’, ‘‘Spacecraft’’ On-Board Systems or Equipment, and Terrestrial Equipment | |
| 10/5/2020 | 9A012 | Non-military ‘‘Unmanned Aerial Vehicles,’’ (‘‘UAVs’’), unmanned ‘‘airships’’, related equipment and ‘‘components’’, as follows (see List of Items Controlled). | |
| 10/5/2020 | 9A515 | ‘‘Spacecraft’’ and Related Commodities |
DD2345 Form
The DD 2345 Militarily Critical Technical Data Agreement is a certification required by U.S. contractors (universities) that wish to obtain access to unclassified technical data disclosing militarily critical technology with military or space application. This data is under the control of, or in the possession of, the U.S. Department of Defense (DoD).
- Unclassified Militarily Critical Technical Data (MCTD) is data that can be used to produce military or space equipment and related technology. also includes such things as, ITAR information, blueprints, drawings, computer software and operating instructions and technical information.
The University of Nebraska-Lincoln (UNL) holds one general DD2345 certification. As per guidelines regarding these certifications, Institutions of Higher Education are supposed to hold only one certification (i.e. to avoid multiple researchers or PI’s applying and utilizing separate or inaccurate certifications). The ECCP staff and empowered official serve as the data custodians for this certification. Those outside of the ECCP shall not hold or apply separately for another DD2345 without communication and/or agreement from the UNL empowered official.
In order to access UNL’s DD 2345 form information, please read and complete the Request for Use Form.
Deemed Export
In addition to the shipment of a commodity (e.g. a product) from the United States to a foreign country, the Export Administration Regulations state that the release of controlled technology to foreign persons in the U.S. are “deemed” to be an export to the person’s country or countries of nationality and is found in 734.2(b) of the EAR.
Note: Those organizations having persons with permanent residence status, U.S. citizenship, and persons granted status as “protected individual,” are exempt from the deemed export rule.
Many of the licenses for deemed exports involve those conducting scientific research. Note that under 734.8 of the EAR, fundamental research is defined as “basic and applied research in science and engineering where the resulting information is ordinarily published and shared broadly within the scientific community” and, as such, is exempt from EAR licensing 5 requirements. Research conducted using publically available information is also exempt from any license requirements.
In addition, Per Part 772 of the Export Administration Regulations (EAR), “technology” is specific information necessary for the “development,” “production,” or “use” of a product. The General Technology Note states that the “export of technology,” is controlled according to the provisions of each Category.” It further states that “technology required for the development, production, or use of a controlled product remains controlled even when applicable to a product controlled at a lower level.” Please note that the terms “required,” “development,” “production,” “use,” and “technology” are all defined in Part 772 of the EAR. Controlled technology is that which is listed on the Commerce Control List.“Use”. (All categories and General Technology Note)
Operation, installation (including on site installation), maintenance (checking), repair, overhaul and refurbishing. “Development”. (General Technology Note)“Development” is related to all stages prior to serial production, such as: design, design research, design analyses, design concepts, assembly and testing of prototypes, pilot production schemes, design data, process of transforming design data into a product, configuration design, integration design, layouts.“Production”. (General Technology Note) (All Categories) Means all production stages, such as: product engineering, manufacture, integration, assembly (mounting), inspection, testing, and quality assurance.
Note: In general, it is difficult for a deemed export to occur under the “use” definition of equipment in the EAR because it must meet all of the above noted categories of use. A foreign person involved in the “development” or “production” of a dual use item, is more likely to meet the deemed export parameters, in which case a deemed export license may be required.
Dual Use
Dual use describes tangible items, software, and/or technology that have both a potential civilian and military use. Determining whether or not an item could fall under the dual use definition should be made in consultation by the ECCP staff as the details of the item can have significant impact in understanding whether or not it is dual use.
Note: For example, an iPad can be used in a classroom (civilian use) and also function as a weapons control system (military use).
Dual-Use Research of Concern (DURC) and Pathogen with
Enhanced Pandemic Potential (PEPP)
The Office of Science and Technology Policy (OSTP) under the United States Government (USG) has created a new policy “United States Government Policy for Oversight of Dual Use Research of Concern and Pathogens with Enhanced Pandemic Potential”. This new policy supersedes the 2012 United States Government Policy for Oversight of Life Sciences Dual Use Research of Concern (Federal DURC Policy) the 2014 United States Government Policy for Institutional Oversight of Life Sciences Dual Use Research of Concern (Institutional DURC Policy) and the Recommended Policy Guidance for Departmental Development of Review Mechanisms for Potential Pandemic Pathogen Care and Oversight. This new policy was published May 2024 with an effective date of May 2025.
The purpose of this policy is to provide an oversight framework for conducting and managing certain federally funded life sciences research on biological agents and toxins. Specifically, when they are enhanced, have the potential to pose risks to public health, agriculture, food security, economic security, or national health. The overarching goal of the policy is to require institutions receiving federal funding to establish policies, practices, and procedures to identify potential DURC and ensure development and implementation of risk mitigations plans for such experiments. *This policy may also affect non-funded research. *
The following agents and toxins are listed by the select agent regulatory agency. This list may change, so please refer to 9 CFR 121.3-121.4, 42 CFR 73.3–73.4, and 7 CFR 331.3, USDA or HHS websites and Section 4.1.1 and 4.1.2 of the Oversight of Dual Use Research of Concern and Pathogens with Enhanced Pandemic Potential Policy. The seven groups below of Select Agents and Toxins are part of this new policy.
HHS Select Agents and Toxins
Biological agents and toxins listed in this part of the list are controlled by Select Agent Regulations, please refer to the Select Agents and Toxins list for any relevant strain exclusions.
Abrin
Bacillus cereus Biovar anthracis
Botulinum neurotoxins
Clostridium botulinum and neurotoxin-producing species of Clostridia
Conotoxins (Short, paralytic alpha conotoxins containing the following amino acid sequence X1CCX2PACGX3X4X5X6CX7)
Coxiella burnetii
Crimean-Congo hemorrhagic fever virus
Diacetoxyscirpenol
Eastern equine encephalitis virus
Ebola virus
Francisella tularensis
Lassa fever virus
Lujo virus
Marburg virus
Mpox virus Clade I
1918-1919 H1N1 including reconstructed replication competent forms of the 1918 pandemic influenza virus containing any portion of the coding regions of all eight gene segments (Reconstructed 1918 Influenza virus)
Ricin
Rickettsia prowazekii
Severe acute respiratory coronavirus (SARS-CoV)
SARS-CoV/SARS-CoV-2 chimeric viruses resulting from any deliberate manipulation of SARS-CoV-2 to incorporate nucleic acids coding for SARS-CoV virulence factors
Saxitoxin
Chapare virus
Guanarito virus
Junín virus
Machupo virus
Sabía virus
Staphylococcal enterotoxins (subtypes A, B, C, D, E)
T-2 toxin
Tetrodotoxin
Tick-borne encephalitis complex virus: Far Eastern subtype
Tick-borne encephalitis complex virus: Siberian subtype
Kyasanur Forest disease virus
Omsk hemorrhagic fever virus
Variola major virus (Smallpox virus)
Variola minor virus (Alastrim)
Yersinia pestis
Overlap Select Agents and Toxins
List of Agents and Toxins
Bacillus anthracis
Bacillus anthracis Pasteur strain
Brucella abortus
Brucella melitensis
Brucella suis
Burkholderia mallei
Burkholderia pseudomallei
Hendra virus
Nipah virus
Rift Valley fever virus
Venezuelan equine encephalitis virusAdd some description that will expand
USDA Veterinary Services (VS) Select Agents and Toxins
List of Agents and Toxins
African horse sickness virus
African swine fever virus
Avian influenza virus [this is included here as a veterinary select agent in 9 CFR 121.3. Low pathogenicity strains are excluded.]
Classical swine fever virus
Foot-and-mouth disease virus
Goat pox virus
Lumpy skin disease virus
Mycoplasma capricolum
Mycoplasma mycoides
Newcastle disease virus
Peste des petits ruminants virus
Rinderpest virus
Sheep pox virus
Swine vesicular disease virus
USDA Plant Protection and Quarantine (PPQ) Select Agents and Toxins
List of Agents and Toxins
Coniothyrium glycines
Peronosclerospora philippinensis (Peronosclerospora sacchari)
Ralstonia solanacearum
Rathayibacter toxicus
Sclerophthora rayssiae
Synchytrium endobioticum
Xanthomonas oryzae
Other Risk Group 4 Pathogens
Pathogens listed in this part of the list are Risk Group 4 but not controlled by the Select Agent Regulations, please refer to the NIH Guidelines for any relevant strain exclusions.
Tick-borne encephalitis virus complex including Absetterov, Central European
encephalitis, Hanzalova, Hypr, and Kumlinge
Herpesvirus simiae (herpes B or monkey B virus)
Hemorrhagic fever agents and viruses as yet undefined
Other Risk Group 3 Pathogens
Pathogens listed in this part of the list are Risk Group 3 but not controlled by the Select Agent Regulations, please refer to the NIH Guidelines for any relevant strain exclusions.
Bartonella
Brucella
Orientia tsutsugamushi
Pasteurella multocida type B -“buffalo” and other virulent strains
Rickettsia akari, R. australis, R. canada, R. conorii, R. rickettsii, R, siberica, R. typhi (R.
mooseri)
Chikungunya virus except the vaccine strain 181/25
Semliki Forest virus
Flexal virus
Lymphocytic choriomeningitis virus (LCM) (neurotropic strains)
Hantaviruses, including Hantaan virus
Middle East respiratory syndrome coronavirus (MERS-CoV)
Severe acute respiratory coronavirus 2 (SARS-CoV-2)
Japanese encephalitis virus except strain SA 14-14-2
Yellow fever virus
Human influenza A virus H2N2 (1957-1968)
Highly pathogenic avian influenza A virus H5Nx strains within the Goose/Guangdong/96-like H5 lineage (e.g., H5N1, H5N6, H5N8 etc.)
Transmissible spongiform encephalopathy (TSE) agents (e.g., Creutzfeldt-Jacob disease and kuru agents)
Other
Additional Information
Any attenuated pathogen or vaccine strain that is currently excluded from the Select Agent Regulations that exhibits the recovery of virulence at or near the wild-type
Mpox virus clade I/II chimeric viruses resulting from any deliberate manipulation of clade II to incorporate nucleic acids coding for clade I virulence factors
Categories of Research
There are two categories under this policy, Category 1 research is subject to oversight by research institutions and federal funding agencies. Category 2 is subject to oversight by research institutions, federal funding agencies, and their federal department if applicable due to heightened potential for biosafety and biosecurity risks.
Category 1 Research
There are three criteria that must be met:
- Involves one or more of the biological agents and toxins specified in the policy (listed above).
- It is reasonably anticipated to result or does result in one of the experimental outcomes:
- Increase transmissibility of a pathogen within or between host species;
- Increase the virulence of a pathogen or convey virulence to a non-pathogen;
- Increase the toxicity of a known toxin or produce a novel toxin;
- Increase the stability of a pathogen or toxin in the environment, or increase the ability to disseminate a pathogen or toxin
- Alter the host range or tropism of a pathogen or toxin;
- Decrease the ability for a human or veterinary pathogen or toxin to be detected using standard diagnostic or analytical methods;
- Increase resistance of a pathogen or toxin to clinical and/or veterinary prophylactic or therapeutic interventions;
- Alter a human or veterinary pathogen or toxin to disrupt the effectiveness of preexisting immunity, via immunization or natural infection, against the pathogen or toxin; or
- Enhance the susceptibility of a host population to a pathogen or toxin.
- Based on current understanding, the research institution and/or federal funding agency assesses that the research constitutes DURC as specified in 4.1.3
- 4.1.3 Category 1 Risk Assessment
- Based on current understanding, the research can be reasonably anticipated to provide, or does provide, knowledge, information, products, or technologies that could be misapplied to do harm with no — or only minor — modification to pose a significant threat with potential consequences to public health and safety, agricultural crops and other plants, animals, the environment, materiel, or national security as specified in 4.1.3.
- 4.1.3 Category 1 Risk Assessment
Category 2 Research
There are three criteria that must be met:
- It involves, or is reasonably anticipated to result in a Pathogen with Pandemic Potential (PPP) as specified in section 4.2.1
- A PPP, or any pathogen that will be modified in such a way that is reasonably anticipated to result in PPP.
- It is reasonably anticipated to result in, or does result in, one or more of the experimental outcomes or actions listed below:
- Enhance transmissibility of the pathogen in humans;
- Enhance the virulence of the pathogen in humans;
- Enhance the immune evasion of the pathogen in humans such as by modifying the pathogen to disrupt the effectiveness of pre-existing immunity via immunization or natural infection; or
- Generate, use, reconstitute, or transfer an eradicated or extinct PPP, or a previously identified Pathogen with Enhanced Pandemic Potential (PEPP).
- Based on current understanding, the research institution and/or federal funding agency assesses that the research is reasonably anticipated to result in the development, use, or transfer of a PEPP or an eradicated or extinct PPP that may pose a significant threat to public health, the capacity of health systems to function, or national security as specified in section 4.2.3.
Definitions
Click here for expansion of definitions
“Biological agents” are any microorganism (including, but not limited to, bacteria, viruses, fungi, or protozoa), infectious material, or any naturally occurring, bioengineered, or synthesized component of any such microorganism or infectious material, capable of causing:
Death, disease, or other biological malfunction in a human, an animal, a plant, or another living organism;
Deterioration of food, water, equipment, supplies, or material of any kind; or,
Deleterious alteration of the environment.
“Biosafety” is the application of practices, controls, and containment infrastructure that reduces the risk of unintentional exposure to, contamination with, release of, or harm from pathogens, toxins, and other associated biological materials.
“Biosecurity” is the application of security measures designed to prevent the loss, theft, misuse, diversion, unauthorized possession or material introduction, or intentional release of pathogens, toxins, biological materials, and related information and/or technology.
“Dual use research” is research conducted for legitimate purposes that generates knowledge, information, technologies, and/or products that can be utilized for benevolent or harmful purposes.
“Dual use research of concern (DURC)” is life sciences research that, based on current understanding, can be reasonably anticipated to provide knowledge, information, products, or technologies that could be misapplied to do harm with no, or only minor, modification to pose a significant threat with potential consequences to public health and safety, agricultural crops and other plants, animals, the environment, materiel, or national security.
“Institutional Contact for Dual Use Research (ICDUR)” is the official designated by the research institution to serve as an internal resource for application of the Policy as well as the liaison (as necessary) between the institution and the relevant federal funding agency.
“Institutional review entity (IRE)” is the entity established by the research institution to execute the institutional oversight responsibilities described in Section 5.2, with the attributes described in Section 5.2.B.
“Life sciences” is the study or use of living organisms, viruses, or their products, including all disciplines, methodologies, and applications of biology (including biotechnology, genomics, proteomics, bioinformatics, and pharmaceutical and biomedical research and techniques).
“Pathogen with enhanced pandemic potential (PEPP)” is a type of pathogen with pandemic potential (PPP) resulting from experiments that enhance a pathogen’s transmissibility26 or virulence, or disrupt the effectiveness of pre-existing immunity, regardless of its progenitor agent, such that it may pose a significant threat to public health, the capacity of health systems to function, or national security. Wild-type pathogens that are circulating in or have been recovered from nature are not PEPPs, but may be considered PPPs because of their pandemic potential.
“Pathogen with pandemic potential (PPP)” is a pathogen that is likely capable of wide and uncontrollable spread in a human population and would likely cause moderate to severe disease and/or mortality in humans.
“Reasonably anticipated” describes an assessment of an outcome such that, generally, individuals with scientific expertise relevant to the research in question would expect this outcome to occur with a non-trivial likelihood. It does not require high confidence that the outcome will definitely occur, but excludes experiments in which experts would anticipate the outcome to be technically possible, but highly unlikely.
For additional information on the policy please see the links below.
- United States Government Policy for Oversight of Dual Use Research of Concern and Pathogens with Enhanced Pandemic Potential
- Implementation Guidance for the United States Government Policy for Oversight of Dual Use Research of Concern and Pathogens with Enhanced Pandemic Potential
- Common Examples of Category 1 and Category 2 Research on Page. 67 to 76.
- Frequently Asked Questions can in Appendix E(Pg. 78).
Export Control and IBC
UNL faculty and staff planning to conduct research with agents and toxins listed under DURC, will require a Technology Control Plan (TCP) before the research starts. This is in addition to meeting UNL Biosafety Guidelines on Dual Use Research of concern. Please contact the Export Control Compliance Program & Biosafety Officer, to ensure all appropriate approvals are in place and a TCP has been established prior to beginning the project. These two offices work together to ensure the above requirements are met.
Educational Information
Information not subject to the EAR if it is released by instruction in catalog courses and associated teaching laboratories of academic institutions. Certain types of information related to encryption software cannot be considered “educational information” and therefore are subject to the EAR even if they are released “by instruction in catalog courses and associated teaching laboratories of academic institutions.”
Information that is normally taught or released by the university as part of the normal instruction in a catalog course or in an associated teaching laboratory is considered Educational Information and, as provided for under the federal regulations (15 CFR§734.3(b)(iii), is NOT subject to export controls.
Embargoed or Sanctioned Countries with Special Rules
U.S. sanctions programs vary in scope and by country. Some are broad-based and oriented geographically (i.e. Cuba, Iran). Others are “targeted” (i.e. counter-terrorism, counter-narcotics) and focus on specific individuals and entities. These programs may encompass broad prohibitions at the country level as well as targeted sanctions. Special export rules apply to Cuba, Iran, North Korea, Syria, Sudan and other countries with sanctions. Due to the diversity among sanctions, we advise visiting the Office of Foreign Assets Control (OFAC) “Sanctions Programs and Country Information” page for information on a specific program.
University activities that involve any type of transaction (e.g., travel to an embargoed country, transfer of information, data or technology; shipping materials; payment of funds; hosting a visitor etc.) with a Non-U.S. person or entity from an embargoed or sanctioned country may be subject to export controls and in some cases strictly prohibited by the U.S. government. A general or specific export license may be required by OFAC for all research and educational activities to an embargoed or sanctioned country.
For example, the Cuba sanctions regulate personal travel to Cuba, as well as, professional research activity conducted with Cuban institutions here and abroad. That said, the Cuba regulations allow for a broad range of research and humanitarian related activity when approved by license from OFAC or if the activities fall under the “General License” and do not require prior approval.
The Iran sanctions (Iranian Transactions and Sanctions Regulations- ITSR), in contrast, do not regulate individual travel to Iran, but remain highly restricted as to any activity or research, which OFAC defines as a “service” to Iran. While, certain kinds of collaborative activities are permissible with Iranian institutions, many are prohibited. Research that contemplates the exchange of material items with Iran, providing guidance or advice on the nuclear or energy sector, attending a conference, or providing advice on establishing a laboratory or research facility in Iran, are examples of services where a license may be required. Likewise, peer review or editorial comment that extends beyond the scope of what is normally defined as credential input or scientific journal editorial review may also trigger a license requirement.
Collaboration with former students or others living in Iran may require a license, as noted previously some activities may be permissible, such as the “Publishing exemption” which allows US persons to engage in a transaction “necessary and ordinarily incident to the publishing and marketing of manuscripts, books, journals, and newspapers in paper or electronic form.” (31 CFR 560.538). However, this exemption cannot be used if the other parties represents the Government of Iran or identified on a restricted party list. Before engaging in collaboration, contact the Export Control Office.
With respect to Syria and Sudan, travel and transactions with these countries will also trigger a review because of the geopolitical instability in both countries, transactions with those nations similarly, must be evaluated carefully for evolving sanctions and requirements.
Special requirements also extend to individual and entities in other countries, such as North Korea; Libya; Crimea region of Ukraine; Russia; Venezuela and a few others. Hence, when contemplating any research or transactional activity with one of these OFAC countries or foreign nationals known to reside in these countries, contact the Export Control Office for an export control review and information on license requirements before proceeding. If a specific OFAC license is required, the Export Control Office can assist; however, it may take months to receive an approval from the US government or may not be approved at all.
Export Control Compliance Policies
Entities on the Restricted List
The U.S. Government periodically publishes laws, regulations, executive orders, or directives that identify entities, companies or persons that are prohibited or restricted from engaging in specific transactions or activities. These restrictions can apply to the activities of institutions of higher education. Activities such as travel, research collaboration, providing or receiving services, and/or hosting visitors from entities will require a review by the Export Control Compliance Office (ECCP) prior to engaging in any activities with them.
These lists are constantly being revised by the U.S. Government, please follow the links for each regulatory list or contact UNL Export Control for questions.
BIS Entity List:
The Export Administration (EAR) contains a list of names of certain foreign persons, which includes private and public: businesses, institutions, educational institutions, and government organizations. Individuals or Entities listed on this list may be subject to license requirements or other export control requirements. For more information click the link above.
BIS Unverified List:
This list is maintained by the Export Administration, and the regulations focus on shipping items to an individual or entity on the list. For more information click the link above.
OFAC Specially Designated Nationals and Blocked Persons (SDN) (OFAC):
This list contains individuals and companies owned or controlled by, or acting for or on behalf of, targeted countries. Specially Designated Nations or SDNs are also listed here. For more information click the link above.
Bureau of International Security & Nonproliferation (ISN) Nonproliferation Sanctions (NPS):
The United States imposes sanctions under various legal authorities against individuals or entities that engage in proliferation activities. For more information click the link above.
See also the guidance topic United States Restrictions and Sanctions Related Lists.
Export
To send or take controlled tangible items, software or technology out of the United States in any manner, to transfer ownership or control of controlled tangible items, software or technology to a foreign person, or to disclose information about controlled items, software or information to a foreign government or foreign person. The controlled tangible item, software or technology being sent or taken out of the United States is also referred to as an “export.”
Export Administration Regulations (EAR)
Federal regulations that regulate the export and re-export of most commercial items. These items can range anywhere from a simple pencil to large equipment. UNL faculty, staff, and students must be cognizant in understanding whether or not their items are controlled via an ECCN or if it is categorized as the lowest set of controls via EAR 99.
See also the guidance topic on Commerce Control List, ECCNs, & EAR 99.
Export Controls
Federal regulations that restrict the release of certain items, information and software to foreign nationals in the United States and abroad. Those regulations are the Export Administration Regulations (EAR) and International Traffic in Arms Regulations (ITAR), as well as regulations administered by the Office of Foreign Assets Control (OFAC).
Export Controls & Biological Agents and Toxins
The United States (U.S.) Department of Commerce, and the State Department, along with various other government agencies control certain technology, items, etc. Authorization from one or more government agencies may be required to transfer export-controlled items internationally. Please also keep in mind that every export from the United States is an import to another country. That country may also have import regulations, duties and taxes that must be followed.
Additionally, foreign national (e.g. F-1, J-1, H1-B, B-1 visa holder or foreign entity) access or use of export-controlled items, in the U.S. may be restricted unless authorized by the federal government.
EAR-Controlled Biologicals
The Bureau of Industry and Security Export Administration Regulations (EAR) controls certain biological pathogens, toxins, and chemical agents through the Commerce Control List (CCL). Faculty and staff planning to transfer biological agents outside the U.S. or to a foreign national in the U.S. are encouraged to seek guidance from the Export Controls Office before engaging in such activities. Several relevant export control classification numbers (ECCN) from the CCL1 are:
- ECCN 1C350 – Chemicals that may be used as precursors for toxic chemical agents;
- ECCN 1C351 – Human and animal pathogens and “toxins” (including, but not limited to, viruses like the Western equine encephalitis, bacteria like the Brucella abortus, and toxins like Shiga toxin;
- ECCN 1C353 – Genetic elements (including, but not limited to chromosomes, genomes, plasmids, transposons, and vectors) and genetically modified organisms associated with the pathogens and toxins;
- ECCN 1C354 – Plant pathogens (including, but not limited to, bacteria such as Xanthomonas albilineans, fungi such as Magnaporthe oryzae);
- ECCN 1E351 – Technology for the disposal of the listed biologicals;
- ECCN 1C991 – Vaccines, immunotoxins, toxin based products (includes medical products, diagnostic and food test kits with toxins);
- ECCN 2B352 – Biological Processing Equipment (including, but not limited to, certain centrifugal separators cable of the continuous separation of pathogenic microorganisms, certain equipment designed for fixed installation in containment facilities).
ITAR-Controlled Biologicals
It is important to keep in mind that biological agents may also be controlled under the International Traffic in Arms Regulations (ITAR) (see Category XIV: Toxicological Agents Including Chemical, Biological Agents and Associated Equipment, of the United States Munitions List) . Foreign nationals and entities in the United States may not access ITAR-controlled biologicals without authorization from the government. ITAR treats any of the following as defense articles:
- “Biological agent or biologically derived substance specifically developed or modified to increase its capability to produce casualties in humans or livestock or to degrade equipment or damage crops.”
- “Equipment and its components, parts, accessories, and attachments specifically designed or modified for military operations and compatibility with military equipment.” Note that equipment used with biological materials may be included under this category.
Fundamental Research and Published Information Exclusions
Generally, in the United States, a foreign national may use EAR export-controlled pathogens and toxins for fundamental research so long as the technology being shared with the foreign national or entity is publicly available and part of fundamental research (see below). It is important to keep in mind that unlike EAR controlled pathogens and toxins, foreign nationals and entities in the United States may not access ITAR controlled biological agents/substances (see Category XIV: Toxicological Agents Including Chemical, Biological Agents and Associated Equipment, of the United States Munitions List (USML)).
Fundamental research is defined as research in science, engineering, or mathematics, the results of which ordinarily are published and shared broadly within the research community, and for which the researchers have not accepted restrictions for proprietary or national security reasons. Please reference our guidance on Fundamental Research Exclusion (FRE) for further information.
Examples of Potentially Export-Controlled Activities
- Foreign national (e.g. F-1, J-1, H1B, B-1, etc.) visa holder is going to work in a laboratory that conducts research related to export-controlled biologicals or vaccines for diseases in animals, plants and humans.
- Sharing proprietary or non-publicly available information, including how to produce, maintain, quality check, or dispose of biological agents or genetic elements with a foreign national or entity anywhere.
- Shipping an export-controlled biological agent or genetic element internationally (“hand carried” is considered an export).
Common Misconceptions
- Some people believe attenuated strains are not controlled; however, attenuated strains can still be controlled.
- Some people believe minimal quantities are not controlled; however, any quantity of a controlled biological is still controlled.
- Some people believe their research materials and equipment are not controlled if the project is fundamental research, however, the fundamental research exclusion does not apply to physical/tangible items.
- Some people believe that if the biological is no longer subject to the Department of Health & Human Services Center for Disease Control and Prevention – Federal Select Agent Program (https://www.selectagents.gov/), it is also not export controlled, however, these are separate concerns controlled by separate governmental departments. Material that may no longer be regulated under the Select Agent Regulations, may still be regulated under the EAR.
Additional Resources
- BIS FAQ’s – Deemed Exports and Fundamental Research for Biological Items
Export License
An export license is formal approval from a federal regulatory agency to export a controlled item to a specific person in a specific place for a specific purpose. Either the BIS or the DDTC, depending on whether the item is specified on the Commerce Control List or United States Munitions List, respectively, issues export licenses for most controlled items.
When the recipient of an intended export is located in a country subject to a comprehensive embargo, special approval needs to be obtained from OFAC (in addition to any approval required by other agencies). Countries subject to comprehensive embargoes include Cuba, Iran, North Korea, (North) Sudan and Syria. Several other countries are subject to less stringent embargoes, but may still require a license for travel and other transactions.
At UNL, the Export Control staff and empowered official have sole authority to determine whether a particular transaction requires an export license. They also have sole authority to apply for export licenses on behalf of UNL faculty, students, and staff.
Export licenses require very specific answers to the following questions:
- What are you exporting?
- Where are you exporting it to?
- Who will receive it?
- How will they use it?
License applications typically take about 60-90 days to process, so you should plan to contact the Export Control staff as early as possible to determine whether a license is required and begin gathering the necessary information.
Export License Exception
An Export License Exception is a special authorization that allows you to export or re-export, under very specific conditions, items that would otherwise require an export license. Export License Exceptions are detailed in EAR§740.
See Educational Information, Fundamental Research Exclusion, and Published Information Exclusion
Foreign National or Foreign Person
Anyone who is not a “U.S. person.” A “U.S. person” is any one of the following:
- U.S. Citizen
- lawful permanent resident alien (green card holder)
- refugee
- protected political asylee or someone granted temporary residency under the amnesty provision.
Anyone who doesn’t fit into one of these categories is considered a “foreign person.” This means that faculty, staff, and students at UNL with work or student visas are considered “foreign persons” for the purposes of export controls.
More detailed information about the agencies’ respective regulations can be found on the Regulatory Information page.
Depending on the details of a project that a foreign national may be planning to work on, or their country(ies) of citizenship and that country’s current status under U.S. government regulations, some foreign nationals may not be eligible to work on certain projects. ECCP staff can assist in clarifying when this may or may not be applicable.
See also the guidance on Participation in Research by Foreign Nationals.
Note: Any foreign entity not incorporated or organized to do business in the United States falls within the definition of a foreign national. This includes any branch of a foreign government and also can include universities and research laboratories in other countries.
Fundamental Research Exclusion (FRE)
Sometimes, a research project may produce information that would normally be subject to export controls and require an export license in order to be shared with colleagues in or from other countries. However, the results of “fundamental research” projects are specifically excluded from these licensing requirements in most circumstances.
Keep in mind that even if the fundamental research exclusion applies, it applies only to the results of the research. If the conduct of the research includes activities subject to export controls, a license must be obtained before any foreign nationals can participate in those activities.
“Fundamental research” is defined as basic and applied research in science, mathematics, and engineering, where the resulting information is ordinarily published and shared broadly within the scientific community. Under the State Department‘s narrower interpretation, “fundamental research” can only describe information and technology that already is in existence and in the public domain. In order for research data to qualify for the “fundamental research” exclusion from the licensing requirements, it must meet two criteria:
- Research results must be freely publishable; and
- There must be no limitations on access to or dissemination of research results on the basis of national origin.
If either condition is not met, this exception is destroyed and dissemination of the data may require a license. For example, certain terms in a statement of work or research agreement might prevent a project from qualifying for the fundamental research exclusion. These include terms that:
- Grant the sponsor pre-approval rights over publication of research results
- Allow the sponsor to claim resulting research information as proprietary or trade secret
- Prohibit foreign nationals from participating in the project
- Restrict the publication or other dissemination of research results from a given project
UNL’s Export Control staff and empowered official are the only persons authorized to determine whether a research project at UNL qualifies as fundamental research.
International Shipping
In addition to any environmental and biosafety guidelines, all shipments of tangible items to foreign countries are subject to export controls. Sometimes the university must obtain an export license from the Commerce Department or State Department for the shipment. Certain documentation must also be filed with the government before any shipments can be made. Failure to do so may constitute an export violation that could result in severe fines and/or other penalties. Please contact the Export Control Staff prior to negotiating any material transfer agreements (MTAs) or packing any materials for international shipments. The Export Control Staff can help you be certain your shipment meets export and sanction laws.
Click here for an example of the shipping invoice
Related Definitions:
End-use – a detailed description of how the ultimate consignee intends to use the commodities being exported.
End-user – a person abroad that receives and ultimately uses the exported or re-exported items. The end-user is not a forwarding agent or intermediary, but may be the purchaser or ultimate consignee.
International Travel
When traveling abroad, faculty, staff and students at UNL should be familiar with the impact of export control regulations. Researchers need to make sure that any information discussed or items taken out of the U.S. are either not controlled, or if controlled, the proper licenses are in place. University personnel, as individuals, can be held liable for improperly transferring controlled technology. Thus, it is important to review and understand that federal requirements are civil and criminal sanctions, with the ability to assess fines and/or invoke prison sentences for individuals violating the export control and embargo laws. These fines or sentencing consequences are substantial and apply to university personnel as well as the University as an institution.
To ensure you do not run the risk of exporting sensitive information or technology when traveling abroad, or dealing with sanctioned countries, entities or individuals, keep in mind that presentations and discussions must be limited to topics that are not related to controlled items or technologies, unless that information is already published or otherwise in the public domain.
Before sharing technology or information, verify that it falls into one or more of the following categories prior to traveling:
- Research that qualifies for the fundamental research exclusion
- Published information
- Publicly available software
- Educational information
- Patent applications
Depending on your international destination(s), an export license or other government approval may be required for your laptop computer, software or other equipment. There are exceptions for “tools of the trade,” but these exceptions depend on the equipment and the country of your destination. Encryption software in particular is subject to special regulations and more stringent license requirements.
Fortunately, most international travel does not raise any export control concerns. However, there are denied entities in almost every country. The checklist is designed to provide UNL travelers information on applicable export control regulations they will need to follow based on the nature of their activities while traveling as well as verifying any export control restrictions for your foreign destination.
For additional information, please visit our FAQ and caution information page.
International Travel Services
For travel outside the U.S., UNL requires all international travelers to file an electronic travel authorization and use Travel & Transport for flight arrangements. Please visit the University of Nebraska International Travel Resources page for additional information and details about foreign travel policies.
Once you have filed your electronic travel authorization through Concur, you will also receive a notification from NuRamp. If you are traveling to a country with risks, sanctions, embargoes, or concerns, you will need to complete our export control travel checklist. If you are traveling to a country with no identified risks, sanctions etc, you will simply receive an informational email and asked to contact Export Control staff if you are traveling with certain items or have plans that should be reviewed for export control concerns.
Visa Support
UNL faculty and staff traveling abroad can use the International Engagement
Visa Support Webpage to find details about how to secure a visa, and enroll in the US State Department Smart Traveler Enrollment Program (STEP).
Evacuation Coverage for UNL Personnel Traveling Abroad
On February 1, 2015, the University of Nebraska – Lincoln secured blanket international travel coverage for all faculty and staff who travel outside the country on UNL business with the correct visa. Faculty and staff no longer need to purchase this insurance individually. Additional information can be found on the University of Nebraska International Travel site.
Best Practices When Bringing Personal Devices and Accessing UNL Information and Resources
It is best practice if there is unpublished, sensitive, and/or confidential information relating to your UNL work/research to put in place safeguards. Only bring information/applications that are absolutely necessary for you to bring when traveling internationally. Make sure to keep electronic devices in your possession and if not on your person make sure the devices are password protected, in a locked room and if possible, a locked safe. It is best practice to uninstall apps (such as Office Suite apps) used to access unpublished, sensitive, and/ or confidential information before traveling internationally and use the online version instead. If not uninstalling apps, it is good to keep the apps password protected and only use when needed.
International Conferences and Presentations (Remote)
There are a few things to consider before presenting material in a remote setting for conferences, seminars, trade shows, or presentations “outside” the U.S. Although you are not physically traveling or shipping material, United States Export Control Laws and Regulations still apply in many instances to data and information that you may be sharing via a remote setting (e.g. zoom presentation).
In general, if the information that you plan on presenting is already published and found in the public domain, it is usually safe for you to share this information. However, if the classification of the Scope of Work or the material, technology, or methods includes:
- EAR
- The EAR considers information released at an “open” conference, meeting, seminar, trade show, or other open gathering to be published, and so excluded from EAR control
- “Open” is defined as Fundamental research that is basic and applied research in science, mathematics, and engineering, where the resulting information is ordinarily published and shared broadly within the scientific community and all technically qualified members of the public are eligible to attend and attendees are permitted to take notes or otherwise make a personal record of the proceedings and presentations. For more information, please see our information on Fundamental Research Exclusion (FRE)
- You can deliver or present the results of your fundamental research in the EAR scope at open conferences, and you can present or deliver other information within the scope of the EAR if you have the right to disclose it (e.g., not constrained by a non-disclosure agreement).
- ITAR
- Information in the scope of the ITAR released by a US person at a conference, seminar, trade show, or exhibition “outside” the US might not be clearly excluded from ITAR control, unless previously or otherwise published in accordance with the ITAR. You can deliver or present the results of your fundamental research in the ITAR scope at open conferences in the US. For more information, please see our information on International Traffic in Arms Regulations (ITAR).
- “Outside” the US, you can deliver or present the following information in the ITAR scope:
- General systems descriptions that ARE NOT considered ITAR technical data (ITAR §120.10(a)(5)).
- Public domain information, such as published research results or material previously released in a university course, at conferences or meetings outside the US.
- Caution: when you answer a question or engage in follow-up discussion, you could be providing a defense service (assisting a non-US person with a defense article), because the information you provide is not in the public domain.
- Items, software, or technical data controlled by ITAR before being received by UNL cannot be released at open conferences.
- OFAC
- Even if the material or technology to be presented is FRE, or the equipment, or items are listed as EAR99/ECCN, a country, institution or entity may be listed on one of the U.S. government’s embargoed/sanctioned countries or part of a restricted parties list such as OFAC’s Specially Designated Nationals list or the Commerce Dept.’s Entity List and be subject to comprehensive sanctions.
Please reach out to the UNL Export Control Personnel for questions regarding international presentations or conferences if your work is not in the public domain or if you will be presenting on material that is Export Controlled, or in a country or an entity (Universities can have restrictions too) with sanctions or embargoes. We can complete a review and screenings to ensure you are not sharing or working with a person/entity with restrictions.
Additional Resouces can be found at:
Tele/Video Conferencing (Zoom/Teams)
UNL Export Control A-Z Guidance (Publicly Available, Public Domain, and Open Source)
International Traffic in Arms Regulations (ITAR)
International Traffic in Arms Regulations (ITAR) are administered by the U.S. Department of State and ITAR places strict controls on the export of “defense articles” and “defense services.” These Federal regulations are used primarily to control the import and export of defense articles and defense services. Similar to ECCNs and EAR 99, another key way in determining whether or not your items/information fall under export control regulations is to understand whether or not they fall under any of the ITAR categories.
These categories are enumerated under the United States Munitions List (USML). USML categories are organized by paragraphs and subparagraphs and identified alphanumerically (e.g. Category IX.10 refers to infrared scene generators, and Category XII.3 refers to laser spot trackers or laser spot detection…”). The categories usually start by enumerating or otherwise describing end-items, followed by major systems and equipment; parts, components, accessories, and attachments; and technical data and defense services directly related to the defense articles of that USML category.
Letter of Attestation
If the department is hiring/hosting non-U.S. person(s), renewing a non-immigrant visa for an employee, hosting visitors, visiting students, or speakers it must be certified that a “No Matching Record” Visual Compliance screening was conducted prior to EC Assessment Approval. If a matching record is found, the department should also recognize that the non-U.S. person may be affiliated with restricted, barred, or concerning entities, institutions, and/or other organizations. This means there are restrictions or due diligence on our ability to share data with or provide access to certain technologies to individuals employed by or affiliated with these restricted, barred, or concerning entities. Additionally, keep in mind that any non-U.S. person(s) receiving funding from a restricted, barred, or concerning entity should be treated as restricted parties themselves, even if they are not individually named on a restricted parties list or list of concern.
One way the university is mitigating the risk of hiring/hosting non-U.S. person(s), renewing a non-immigrant visa for an employee, hosting visitors, visiting students, or speakers who might have an affiliation, or their institution and/or other organizations might show up on a restricted party list or list of concern is through Letters of Attestation (LOA). An LOA is an acknowledgment to the Beneficiary and Supervisor that the Beneficiary has an affiliation with an entity on a Restricted Party List or List of Concern and they cannot export-control information to that entity and should be committed to fundamental research. An LOA is situation specific. When the need for an LOA has been identified, Export Control will contact the Supervisor with the appropriate information needed for them to complete the LOA. The LOA can be found by using the link below:
https://go.unl.edu/ec_loa
Military or Space Related Research
International Traffic in Arms Regulations (ITAR) are administered by the U.S. Department of State. ITAR places strict controls on the export of “defense articles” and “defense services.” Defense articles include any item, software or technical data on the United States Munitions List (USML). Defense services include assistance (including training) or any technical data associated with a defense article furnished to foreign persons, whether or not in the United States. Any defense article, service or related technical data found to be on the USML requires an export license before it can be exported – that is, given to a foreign person, whether or not they are in the United States. Some license exemptions are available under specific circumstances, but in general you should expect to obtain an export license.
ITAR controls exports that are:
- Predominantly items of military nature
- Modified or specifically designed for military use
- “Space” related items and technology
- Controlled for national security reasons
Because spacecraft and satellites are subject to export controls, UNL policy requires a determination or technology control plan (TCP) for almost every research project that studies the design or operation of these items. Certain projects funded by federal agencies, such as NASA, also prohibit the participation of certain foreign persons or entities. Contact the Export Control Staff for more information.
Research into military technologies will also generally require the implementation of a TCP. This includes studies into the design and operation of weapons, defense systems, military vehicles, and protective gear. Almost all military research projects require government approval, so please be sure to contact the Export Control Staff when applying for funding from the Defense Department, Department of Energy, NASA, or the Department of Homeland Security.
NASA Checklist
NASA is restricted by specific applications of Section 1340(a) of The Department of Defense and Full-Year Appropriations Act, Public Law 112-10 (NASA’s 2011 continuing resolution), and Section 539 of the Consolidated and Further Continuing Appropriation Act of 2012, Public Law 112-55 (NASA’s FY 2012 appropriation) from using funding appropriated in the Acts to enter into or fund any grant or cooperative agreement of any kind to participate, collaborate, or coordinate bilaterally in any way with China or any Chinese-owned company, at the prime recipient level or at any subrecipient level, whether the bilateral involvement is funded or performed under a no-exchange of funds arrangement.
NASA defines “China or Chinese-owned Company,” to mean the People’s Republic of China (PRC), any company owned by the PRC, or any company incorporated under the laws of the PRC; this would include Chinese universities and research institutes. The law is interpreted by NASA to prohibit participation (funded or unfunded) by any individual, regardless of nationality, who is affiliated with the Chinese Government or a Chinese-owned Company.NASA does not consider this a prohibition of Chinese nationals.For each NASA proposal or award, UNL must certify compliance with this restriction. When research personnel submit a proposal to NASA, they will be contacted by OSP and RCIS staff in order to complete a NASA Certification form. This form asks a series of questions regarding each person’s involvement with China and requires signature and attestation that the information being disclosed is true. Affirmative disclosures regarding involvement with China will be reported to NASA as part of the proposal/award process. Moreover, PIs are responsible for ensuring that, prior to adding additional participants to a NASA project,or if any changes occur with any project personnel’s involvement with China, the new participants must provide a complete and up-to-date certification to Sponsored Programs and/or an update to previously submitted information. In addition, Export Control and COI purposes necessitated a couple of additional steps beyond the certification form. Please reference the NASA checklist document linked below to review the three specific steps required for these awards.
If any question arise regarding whether or not research personnel should disclose certain information, they must always err on the side of caution and ensure full and transparent disclosure to NASA and to UNL.
The Office of Foreign Assets Control (OFAC)
The Office of Foreign Assets Control (OFAC) of the US Department of the Treasury administers and enforces economic and trade sanctions based on US foreign policy and national security goals against targeted foreign countries and regimes, terrorists, international narcotics traffickers, those engaged in activities related to the proliferation of weapons of mass destruction, and other threats to the national security, foreign policy or economy of the United States. OFAC acts under Presidential national emergency powers, as well as authority granted by specific legislation, to impose controls on transactions and freeze assets under US jurisdiction. Many of the sanctions are based on United Nations and other international mandates, are multilateral in scope, and involve close cooperation with allied governments.
See also the guidance topic Embargoed or Sanctioned Countries with Special Rules.
Open & Closed Meetings
Open meetings are conferences, seminars or other gatherings where all technically qualified members of the public are eligible to attend and attendees are permitted to take notes or otherwise make a personal record of the proceedings and presentations.
This is in contrast to a closed meeting in which not all technically qualified members of the public may attend and often notes or recording of the proceedings or presentations may be prohibited. This is typically due to the nature of the information that will be presented or discussed.
It is particularly important to disclose that you plan on attending a closed meeting if you are traveling internationally or if you will be presenting or provided access to any information that will be export controlled. You should contact ECCP staff prior to participating in a closed meeting, so that they can review whether or not certain security parameters should be put into place regarding your attendance at such a meet.
Online STEM courses to Sanctioned and Embargoed Countries
Export control laws and regulations control the export of tangible and intangible items, materials, information, or services, which may include online learning. Typically, no license is required to share information that is part of an online course. The regulations provide for an educational exemption. The International Traffic in Arms Regulations (ITAR) exempts most sharing of information “commonly taught” in colleges and universities, and the Export Administration Regulations (EAR) usually exempts educational information “released by instruction in catalog courses and associated teaching laboratories”.
However, the Office of Foreign Assets Control (OFAC) regulates instruction delivered online, to individuals who are residents in, or ordinarily resident to, comprehensively sanctioned and embargoed countries in instances when such instruction is considered a “service” (certain exceptions apply). Specific Licenses to provide a “service” to comprehensively sanctioned and embargoed countries are required under most circumstances. Under other circumstances a General License, which authorizes a particular type of transaction without the need to apply for a Specific License is allowable. There may also be licensing requirements for software and other items associated with the online courses.
The ECCP will assess the applicable restrictions summarized in the below guidance chart and explore potential options for requesting U.S Government licensing authorization if/when applicable. This means, if you are planning on delivering an online learning course to anyone residing in or ordinarily resident to one of the below countries, you must contact the ECCP prior to engaging in this activity.
Participation in Research by Foreign Nationals
Foreign nationals are persons who are not U.S. citizens or lawful permanent residents (those who have green cards). A foreign national also means any foreign corporation, business association, partnership or any other entity or group that is not incorporated to do business in the U.S.
The university campus is open to students and faculty from many different countries. However, access to restricted or export-controlled technology, commodities, defense articles and defense services by an unauthorized foreign person could result in severe criminal or civil penalties for the university and the university employee making the export.
When planning research involving foreign countries or foreign nationals (including graduate or undergraduate research assistants), the principal investigator (PI) should understand that, depending upon the nature of the research and the status of the foreign country, obtaining export licenses can take several months. Therefore, the PI must identify any possible export control restrictions in the early planning stages of a proposal and contact the Export Control Staff for assistance in complying with applicable laws.
While UNL strives to maintain an open campus that fosters collaboration between students and faculty from many different countries, allowing unauthorized foreign persons to access controlled items or information, such as export controlled technology, commodities, defense articles, technical data, and/or defense services, can constitute a violation of one or more export control regulations. Prosecution of an export violation may result in fines of up to $1 million and/or a prison sentence of up to 20 years.
Publicly Available, Public Domain, and Open Source
Information that is already published or is out in the public domain is considered public information and, as provided for under the federal regulations (15 CFR§734.7 and 15 CFR§734.11), is NOT subject to export controls (i.e. published information exclusion). However, there are differences between how the ITAR and EAR define this exclusion. While they share the idea that publicly available information should not be subject to export controls, they differ in how the information can be made publicly available. Additionally, the ITAR refers to information “in the public domain” while the EAR refer to “publicly available” information.
Publicly Available (EAR)
- Refers to “publicly available technology and software”, the EAR does not use the expression “public domain”. Publicly available technology and software are excluded from control under the EAR.
- Examples of information in the public domain include:
- Books, newspapers, pamphlets
- Publicly available technology
- Software with open source code that is made publicly available
- Information presented at conferences, meetings, and seminars open to the public
- Information included in published patents
- Websites freely accessible by the public
Public Domain (ITAR)
- Meaning information that is published, and which is generally accessible or available to the public. As referenced in the 22 CFR § 120.11, public domain includes:
- Books, newspapers, pamphlets
- Subscriptions of published information that do not have restrictions
- Information included in published patents
- Unlimited distributions at conferences, seminars, and trade shows open to the public
- Through public release with unlimited distribution in any form, that is approved by a United States department or agency
- Information regarding general scientific, mathematical, or engineering principles commonly taught in schools, colleges and universities is not controlled by ITAR
Open Source
Open Source and Publicly available are commonly confused and used interchangeably. Open Source is available to all users but is restricted by copyright laws as Public Domain Software is not restricted by copyright laws.
- Open source commonly refers to software that for which the original source code is made freely available and may be redistributed and modified.
Purchasing & Export Controls Guidance
When purchasing equipment, software or other tangible items, it is important to ensure that any export control issues are addressed prior to bringing them to campus.
The following guidance provides information for purchasing equipment, software, or other tangible items whether they are from a foreign or U.S. vendor. It also provides questions to ask of vendors when purchasing these type of items, information on anti-boycott language, international shipping for these purchases, and some examples of foreign Universities or other entities that appear on the U.S. government Restricted or Denied listings.
Purchasing & Export Controls Guidance
Re-export
According to the U.S. Bureau of Industry and Security (BIS), a reexport is “the shipment or transmission of an item subject to the Export Administration Regulations (EAR) from one foreign country to another foreign country. A reexport also occurs when there is ‘release’ of technology or software (source code) subject to the EAR in one foreign country to a national of another foreign country.”
This is important to understand if your item, technology or software requires a license before you can export it from the United States to a specific country. That same item, technology or software requires a license to be reexported from its current non-U.S. country to another non-U.S. country (e.g. You are shipping an item from UNL to a lab in France, which then will be shipping that same item to a lab in China).
Restrictions on Publication
Certain terms included in contracts or agreements might prevent a project from qualifying for the fundamental research exclusion. These include terms that:
- grant the sponsor pre-approval rights over publication of research results or
- allow the sponsor to claim resulting research information as proprietary or trade secret
- otherwise restrict the publication or other dissemination of research results from a given project.
When information generated by such a project includes these type of terms, the project would therefore be controlled under export regulations because restrictions on publications void the fundamental research exclusion. Such controls may also result in restrictions on the participation of certain foreign nationals and require licensing. Also, contractual restrictions on participation by foreign nationals might be interpreted to imply restrictions on publication, with a potential loss of the fundamental research exclusion.
Research Related to Nuclear, Chemical, Biological Weaponry; Missiles; or Unmanned Vehicles
Exports of special nuclear material (including Pu, 233U, and 235U) are governed by the Nuclear Regulatory Commission.
Technologies related to the production and use of nuclear material for peaceful purposes, like nuclear energy, are regulated under the Export Administration Regulations and specific items can be found in Categories of the Commerce Control List.
Technologies related to the military use of nuclear energy, including weapons systems, are regulated under the International Traffic in Arms Regulations. Specific controlled technologies can be found in Categories enumerated under the United States Munitions List (USML).
The Department of Commerce regulates and restricts the transfer and export of “dual use” technologies which are technologies or items having both commercial and military or proliferation applications. These can be found listed on the Commerce Control List (CCL).
Some examples of this research:
- Nuclear technologies associated with production and use of nuclear material for both peaceful and military applications, including certain associated technologies related to nuclear physics and/or nuclear engineering.
- Rocket system technologies that contribute to ballistic missile systems, space launch vehicles and sounding rockets and unmanned air vehicles (UAV). The also include navigation, avionics and flight control usable in rocket systems and unmanned air vehicles.
- Chemical, biotechnology and biomedical engineering technologies that could be applied to develop and produce chemical and biological weapons.
- Remote sensing, imaging and reconnaissance technologies related to satellite and aircraft remote sensing that can be used for civilian imagery projects or for military and intelligence reconnaissance activities.
- Advanced computer/microelectronic technology that can play a useful (but not necessarily critical) role in the development and deployment of missiles and missile systems and in the development and production of nuclear weapons.
- Certain materials technologies related to structural functions in aircraft, spacecraft, missiles, undersea vehicles and propulsion devices.
- Information security technologies associated with cryptography and cryptographic systems that help ensure secrecy for communications, video, data and related software.
- Laser and directed energy systems technologies that have critical military applications, including incorporation in guided ordinance such as laser guided bombs and ranging devices.
- Sensors and sensor technologies that provide real-time information and data and could provide a significant military advantage in a conflict.
- Marine technologies used in propulsion systems designed for undersea use and navigation and quieting systems associated with reducing detectability and enhancing operations survivability.
Research Related to Encryption Technologies
Encryption software is software whose main task is encryption and decryption of data, usually in the form of files on hard drives and removable media, or email messages sent over computer networks or the Internet.
Sharing, shipping, transmission or transfer of almost all encryption software in either source code or object code is subject to U.S. export regulations. Even most publicly available “dual-use” encryption code requires a license or license exception to ship outside the U.S.
In addition, U.S. persons are prohibited, without prior authorization, from providing technical assistance (instruction, skills training, working knowledge and consulting services) to a foreign national with the intent to help in the overseas development or manufacture of encryption software subject to U.S. Government notification or authorization. This prohibition does NOT limit university personnel from teaching or discussing general information about cryptography or developing or sharing encryption code within the United States that arises during, or results from, fundamental research.
However, source code for most strong encryption software is subject to export controls. Projects that require access to such source code (either for the purposes of study or development) will likely be required to implement a technology control plan that specifically details information security procedures.
Research Involving Select Agents or Other Pathogens
Both the International Traffic in Arms Regulations (ITAR) and the Export Administration Regulations (EAR) have provisions for the control of pathogens and toxins. The control level depends on which regulations apply to the item.
Inside the United States any person, including foreign nationals, may purchase and use EAR export controlled pathogens and toxins for fundamental research. However, the “deemed” export rule applies to technical information about the controlled item or to the development or production of technology associated with the controlled item. For example, if a PI receives confidential, proprietary or export controlled information about the development or production of an EAR controlled biological, the PI may need a “deemed” export license to provide such information to a foreign national on campus.
Select agent regulations are separate from export control regulations, any given research project may be subject to either or both sets of regulations. This means that labs handling select agents may be required to complete both an IBC protocol and in some cases a determination or technology control plan may be required.
If a PI wishes to ship controlled pathogens or toxins outside the U.S. please Contact the Export Control Staff as an export license may be required.
Restricted Party Screening (RPS)
The United States Government prohibits U.S. persons, including educational institutions, from conducting business with persons and entities designated as restricted parties (Specially Designated Nationals and Blocked Persons – SDNs) on any federal restricted party listings. In addition, some entities may also be added to what is call the “unverified listing,” which is a listing of f0reign entities in which the U.S. government has concerns but has not yet designated them as a restricted party.
The Office of Foreign Asset Controls (OFAC) is the central repository for many of these restricted party or unverified lists. However, the lists are also administered and enforced by several additional U.S. agencies which include but are not limited to:
- Department of Commerce
- Department of State,
- Department of Treasury,
- FBI
- Department of Homeland Security
The University of Nebraska-Lincoln utilizes a specialized software subscription service for screening of entities and individuals against the restricted party or unverified database listings maintained by the above listed agencies. This software, called Visual Compliance, not only permits screening against all the federally maintained lists, but also auto-updates all prior screenings on a nightly basis in the event of changes to any of the restricted party or unverified listings. Screenings can be completed quickly and easily by ECCP staff, typically within the same day of the request. In many instances, such as export controlled research and foreign national visa reviews, ECCP staff are already completing screenings of entities and individuals. However, UNL personnel can and should request screenings be completed under additional circumstances such as:
- Tours involving foreign nationals or entities on campus. Particularly if a tour will involve R&I and research areas that could have or has been designated as working in an export controlled area.
- International collaborations
- Research protocols that will involve an international component.
- International shipments
To request a screening using the Visual Compliance software, please contact ECCP staff directly. When requesting a screening, please be prepared to provide some of the following information in order for staff to complete the screening(s):
- Person or Entity Name
- Country(ies) of citizenship or country where the entity is located
- Reason for screening (e.g. campus tour)
Additional Resources
- Department of Commerce Guidance on Restricted Party Screening;
- Department of the Treasury Guidance on Restricted Party Screening; and,
- Export.gov Information and Links to Consolidated Screening Lists.
Safeguarding Covered Defense Information, Controlled Unclassified Information & Office 365 US Government
Information that falls under CDI requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Government-wide policies that resides on the contractor’s information system, government wide policy, and is:
- Marked or otherwise identified in the contract, task order, or delivery order and provided to the contractor by or on behalf of DoD in support of the performance of the contract; or
- Collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract.
These controls must be compliant with the below federal regulations:
- 32 CFR Part 2002: Issued by the Federal Information Security Oversight Office (ISOO) to establish policy for agencies on designating, safeguarding, disseminating, marking, decontrolling, and disposing of CUI, self-inspection and oversight requirements. The rule affects Federal executive branch agencies that handle CUI and all organizations (sources) that handle, possess, use, share, or receive CUI—or which operate, use, or have access to Federal information and information systems on behalf of an agency.
- DFARS 252.204.7012 Safeguarding Covered Defense Information (CDI) & Cyber Incident Reporting. This clause is found in DOD Contracts, which addresses the requirements of safeguarding and reporting breaches.
- NIST SP 800-171 Set of Information Technology Security standard guideline required for “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations,” provides requirements for protecting the confidentiality of Controlled Unclassified Information (CUI). The requirements apply to all components of nonfederal information systems and organizations that process, store, transmit CUI, or provide security protection for such components. The CUI requirements are intended for use by federal agencies in contractual vehicles or other agreements established between those agencies and nonfederal organizations.
- NIST SP 800-171 identifies 110 unique requirements that apply to University information systems that process, store, or transmit CUI.
At UNL, Office 365 US Government is the current solution that has been implemented to meet the NIST 800-171 IT security requirements. Office 365 US Government is a Microsoft Office (Word, Excel), email (Outlook) and storage platform that meets U.S. Government security standards. The below list of security features does not include everything covered by this platform, but some of the main features allow UNL researchers to:
- Store content in the continental United States.
- Support covered defense information and export-controlled data.
- Support protected health information with HIPAA business associate agreements.
If your project requires adherence to CUI or CDI requirements, please be aware that there is a cost associated with receiving access to use the secure Microsoft 365 US Government platform. Please ensure you are consulting with RICS/OSP/ITS regarding planning for this cost during the proposal stage if your research project will require this type of security.
If CUI or CDI compliance is required for a research project, RCIS and/or OSP will work with the Principal Investigator and Information Technology Services (ITS) to:
- Verify that the research project will receive, possess, and/or create CUI or CDI.
- Identify, with assistance from ITS, the appropriate information security system/technology solution to use to secure and store the information.
- Appropriate system solutions may include Microsoft Office 365 US Government or use of encrypted/secure email and storage.
- Communicate an appropriate information security plan for the research project. This plan outlines the policies and procedures the research team will follow (e.g., information access restrictions, laboratory security, etc.) to comply with the CUI or CDI requirements.
Questions to Consider:
- Does your research project receive funding from the Department of Defense (DoD) or a DoD-funded prime contractor?
- Does the contract contain DFARS 252.204.7008, 7009 and 7012 clauses, on safeguarding covered defense information and cyber incident reporting? The following is an example/part of a clause that could be contained in a contract:
- The covered contractor’s information system shall be subject to the security requirements in National Institute of Standards and Technology (NIST) Special Publication (SP) 800-171, “Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations” (available via the internet at http://dx.doi.org/10.6028/NIST.SP.800-171) in effect at the time the solicitation is issued or as authorized by the Contracting Officer.
- Have you been informed that you have a project funded by a non-DoD sponsor subject to DFARS 252.204.7008, 7009 and 7012 or NIST 800-171?
- Does your project involve funding from DoD’s Small Business Innovation Research (SBIR) or Strategic Technology Transfer Research (STTR) programs?
- Does the project result in storing, accessing, processing, or transmission of CUI/CDI?
Note: the Cybersecurity Maturity Model Certification (CMMC) is a new cybersecurity certification that will be required by Department of Defense contractors in the US Defense Industrial Base, university-based research labs & facilities, University Affiliated Research Centers (UARCs) and Federally Funded R&D Centers (FFRDCs). The CMMC is a unified standard for implementing cybersecurity across the defense industry base, which include universities that conduct research funded under DoD. CMMC requires that contractors be audited by 3rd party organizations to determine their current cybersecurity maturity level (1-5). The DFARS clause 252.204-7012 is currently viewed as a “trust measure,” while CMMC will be a “verification measure.”
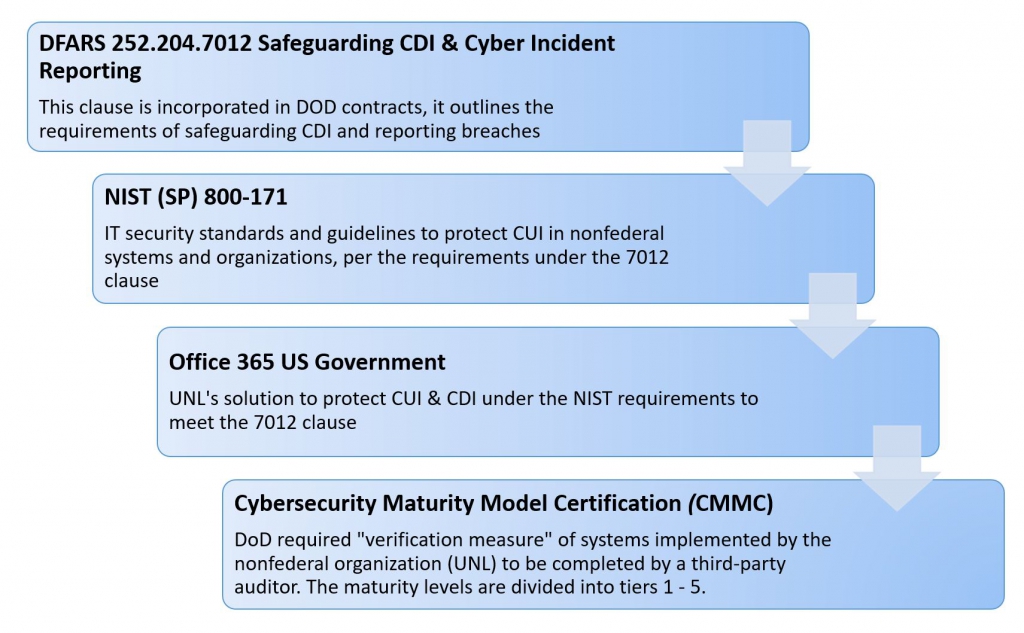
See also guidance topic on Controlled Unclassified Information (CUI) & Covered Defense Information (CDI).
Student Theses/Dissertations & Export Controls
In general, most student involvement in research or other academic activities will not fall under export control regulations. However, in some circumstances, students may be working towards a graduate degree in an area where export controls apply. While this can be a valuable learning experience as part of the student’s graduate work, faculty advisors must closely weigh how export control requirements (e.g. publication restrictions) will impact the student’s ability to complete the project and meet academic or graduation requirements. This guidance is intended to provide information to students and faculty regarding student involvement and the parameters around graduate work that is subject to export control requirements.
In addition to following all requirements as outlined within an export control determination or TCP, the below listing provides frequently encountered areas that must be considered by the student and the faculty member(s). When a student thesis/dissertation will be involved, the faculty must ensure notification to the ECCP occurs as early on in the process as possible. Without this notification, it is difficult to ensure appropriate review, documentation, and export control requirements are met well ahead of the project starting and the student graduating.
- PIs: Due to security concerns, students are not allowed to be listed or function as the PI on any export-controlled project. The involved faculty member/advisor is ultimately responsible for the project and must be listed as the Principal Investigator (PI). Instead, students should be listed as the Secondary Investigator (SI) if the project is specific to their thesis/dissertation work.
- Publication/Foreign National Restrictions: If publication and/or foreign national restrictions are applicable to the project:
- The final publication of the student thesis/dissertation may be embargoed for a certain period of time, or permanently, given the sensitivity of the work.
- The PI must notify the Office of Graduate Studies as soon as they are aware publication restrictions are applicable to a student thesis/dissertation. This notification is to ensure Graduate Studies can appropriately manage and embargo the information.
- For High Risk/ITAR controlled projects that involve restrictions on foreign nationals, only the minimum amount of information and people must be notified and/or have access to the information in Graduate Studies. The person(s) identified in Graduate Studies must be vetted and approved by the Export Control Compliance Program (ECCP) prior to the thesis/dissertation information being provided.
- Committees/Presentations: When certain High Risk/ITAR controlled projects or foreign national restrictions are involved, the ECCP must review and approve anyone selected to be part of the student’s committee. In addition, when the final thesis/dissertation will be presented, these same restrictions will govern whether or not the presentation can be open to the public or if it must be closed and only involve approved individuals. The faculty and student must ensure that this information is understood and provided to the ECCP for vetting/approving individuals.
- Printing/Dissemination: Typically, students want to ensure the final version of their thesis/dissertation is printed or disseminated. However, in the above cases, unless the sponsor of the project and/or ECCP has reviewed and approved the release of the information/publication restriction, the student will not be allowed to print or distribute final copies of their thesis/dissertation.Students and faculty must ensure that publication restrictions are closely followed, and that information is not released prior to receiving approval.
Technical data
Technical data is a specific term defined under the ITAR that refers to information that is required for the design, development, production, manufacture, assembly, operation, repair, testing, maintenance or modification of defense articles. Technical data includes, but is not limited to, information in the form of:
- Blueprints, engineering scale drawings, photographs, plans, instructions and documentation for defense article;
- Information covered by an invention secrecy order or certain kinds of classified information;
- Generated by independent R&D for military application;
- Generated under a DoD contract;
- Provides understanding of sensitive capabilities (e.g. stealth characteristics), or vulnerabilities (e.g. EMI problems);
- Extracted complete section from technical documents directly relating to defense articles or defense services;
- Software directly related to defense articles.
The term “technical data” does not include information concerning general scientific, mathematical or engineering principles commonly taught in schools, colleges and universities. It also does not include information in the public domain or basic marketing information on function, purpose, or general system descriptions.
Keep in mind that the “technical data” term, can appear in contracts and agreements that may not have the same meaning as the technical data definition under ITAR. The type of research and sponsor is a good indicator on whether the term refers to information related to defense articles or other type of information.
UNL faculty, staff and students conducting research that will generate, access or store technical data, as defined under the ITAR, will require a Technology Control Plan (TCP), as this information is linked to defense articles and defense services. Note, UNL is not a cleared facility, therefore, technical data that is considered “classified” information cannot be accessed or received on campus.
See also the guidance topic International Traffic in Arms Regulations (ITAR).
Technology
Per the Export Administration Regulations (EAR), “technology” is information necessary for the “development,” “production,” or “use” of an item. Technology goes beyond the general and basic marketing material, or information contained in published information such as manuals; the term refers to specific information that may come in the form of blueprints, drawings, plans, diagrams, models, methods, engineering specifications or other documentation linked to dual-use items identified in the Commerce Control List (ECCNs on the CCL). Therefore, the level of controls will depend on the nature of the technology and the country of origin of the foreign national. The “deemed export” rules apply to the transfer of such technology, to a foreign national inside the U.S.
When there are dual-use items, the export control office reviews the possibility of a deemed export of knowledge and technology. For the use of equipment, a deemed export would only occur if ALL 6 categories of “use” of equipment by a foreign national are met, which are defined as: operation, installation, maintenance (checking), repair, overhaul and refurbishing (restore, review).
- For example, a foreign national who is operating a commercial laser or optical equipment in a lab classified under ECCN 6A005 on the CCL, would only have access to the information of “operation,” which can be found in the user manual. The foreign national is not meeting all categories of “use,” and there is no transfer of technology and therefore, no deemed export. On the other hand, if a foreign national is involved in the “development” (e.g., engineering specifications, design, blueprints) of a new laser that meets the parameters of ECCN 6A005, this would constitute a transfer of technology requiring further review to assess the level of control of the dual-use item and to determine of a deemed-export license is required.
See also guidance topic Export Administration Regulation (EAR), Deemed Export and Dual-Use.
U.S. Restrictions and Sanctions Related Lists (Consolidated Screening List)
While the UNL Export Control Compliance Program uses Visual Compliance, a software that screens from multiple listings that includes the consolidated screening listings, the following information and resources are available for public use.
The Consolidated Screening List (CSL) is a list of parties for which the United States Government maintains restrictions on certain exports, reexports, deemed exports or transfers of items. Each agency is responsible for maintaining and updating their respective lists. Companies, entities, and persons found on the lists are sanctioned by the U.S. government and may not export goods from the United States or receive exported goods from the United States. Exporters are responsible for ensuring that all export transactions are properly authorized.
These tools are a consolidation of multiple export screening lists of the Departments of Commerce, State and the Treasury and may be used as an aid to in conducting electronic screens of potential parties to regulated transactions.
In the event that a company, entity or person on the list appears to match a party potentially involved in your export activity or transaction, you must contact the Export Control Office in order to ensure appropriate follow up is completed. There may be a strict export prohibition, requirement for seeking a license application, evaluation of the end-use or user to ensure it does not result in an activity prohibited by any U.S. export regulations, or other restriction.
Definitions
- Denied Persons List (DPL) – Individuals and entities that have been denied export privileges. Any dealings with a party on this list that would violate the terms of the denial order are prohibited.
- Unverified List – End-users who the U.S. Bureau of Industry and Security (BIS) has been unable to verify in prior transactions. The presence of a party on this list in a transaction is a “Red Flag” that should be resolved before proceeding with the transaction.
- Entity List – Parties whose presence in a transaction can trigger a license requirement supplemental to those elsewhere in the Export Administration Regulations (EAR). The list specifies the license requirements and policy that apply to each listed party.
- Nonproliferation Sanctions (NSP) – Parties that have been sanctioned under various statutes. The list is updated as appropriate, but the Federal Register is the only official and complete listing of nonproliferation sanctions determinations.
- AECA Debarred List – Entities and individuals prohibited from participating directly or indirectly in the export of defense articles, including technical data and defense services. Pursuant to the Arms Export Control Act (AECA) and the International Traffic in Arms Regulations (ITAR), the AECA Debarred List includes persons convicted in court of violating or conspiring to violate the AECA and subject to “statutory debarment” or persons established to have violated the AECA in an administrative proceeding and subject to “administrative debarment.”
- Specially Designated Nationals (SDN) List – Parties who may be prohibited from export transactions based on OFAC’s regulations. The EAR requires a license for exports or reexports to any party in any entry on this list that contains any of the suffixes “SDGT” (Specially Designated Global Terrorists), “SDT” (Specially Designated Terrorist), “FTO” (Foreign Terrorist Organization), “IRAQ2” (Iraq Related Sanctions), or “NPWMD” (Nonproliferation and Weapons of Mass Destruction).
- Foreign Sanctions Evaders (FSE) List – Foreign individuals and entities determined to have violated, attempted to violate, conspired to violate, or caused a violation of U.S. sanctions on Syria or Iran, as well as foreign persons who have facilitated deceptive transactions for or on behalf of persons subject to U.S. Sanctions. Transactions by U.S. persons or within the United States involving Foreign Sanctions Evaders (FSEs) are prohibited.
- Sectoral Sanctions Identifications (SSI) List – Individuals operating in sectors of the Russian economy with whom U.S. persons are prohibited from transacting in, providing financing for, or dealing in debt with a maturity of longer than 90 days.
- Palestinian Legislative Council (PLC) List – Individuals of the PLC who were elected on the party slate of Hamas, or any other Foreign Terrorist Organization (FTO), Specially Designed Terrorist (SDT), or Specially Designated Global Terrorist (SDGT).
- Correspondent Account or Payable-Through Account Sanctions (CAPTA) List – Foreign Financial Institutions Subject to CAPTA. As of March 14, 2019, the List includes one foreign financial institution subject to correspondent or payable-through account sanctions. Prior to March 14, 2019, this entity was on OFAC’s Part 561 List.






